In the high-stakes world of Web3 bounties, where developers chase rewards for complex tasks like AI model inferences, speed is everything. Traditional zero-knowledge proofs grind to a halt on massive machine learning models, turning fast bounty proof generation into a pipe dream. Enter model slicing techniques: a game-changer for efficient zkML verification that chops bloated computations into lean, provable chunks. At zkverifiedtasks. com, we're leveraging these methods to slash verification times, ensuring bounty hunters get paid without the wait.
Picture this: a bounty requires verifying a transformer model's output on sensitive data. Full-model zk proofs demand gigabytes of memory and hours of prover time. Model slicing flips the script by partitioning the model into parallelizable slices, each generating its own succinct proof. Aggregate them on-chain, and you've got distributed zk proofs tasks that scale effortlessly. This isn't theory; recent breakthroughs like DSperse and TeleSparse are making it reality, fueling platforms like ours with cryptographic speed.
Why Model Slicing Crushes Traditional zkML Bottlenecks
Zero-knowledge machine learning has promised privacy-preserving verification forever, but reality bites. Proving an entire neural net inference? It's a computational black hole, especially for bounty verification where tasks pile up. Slicing attacks this head-on by isolating layers or sub-modules, proving only what's necessary. I love how it mirrors swing trading: focus on high-momentum setups, ignore the noise.
Key Benefits of Model Slicing
- Reduced Prover Time: Slices complex models into manageable parts for faster proof generation, as in TeleSparse, slashing verification delays in zk bounties.
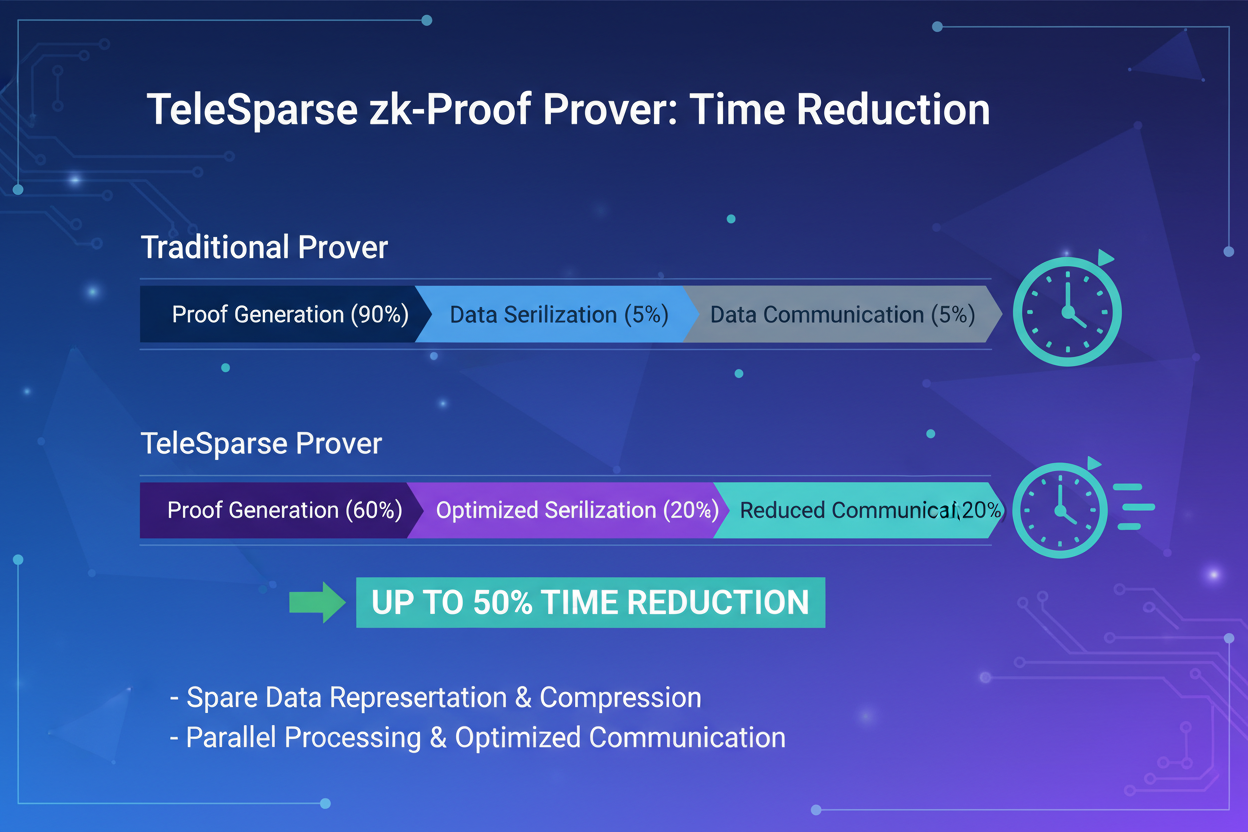
- Lower Memory Use: Optimizes circuit constraints via sparsification and teleportation, minimizing prover memory like in TeleSparse for efficient large model handling.
- Parallel Processing: Enables distributed inference and targeted subcomputation verification with DSperse, speeding up Web3 bounty tasks.
- Seamless Scalability: Supports scalable strategies for diverse deployments, ensuring low-latency verification for growing Web3 applications like ZKLoRA.
Take bounty hunters submitting AI task proofs. Without slicing, fraudsters spam junk; with it, legitimate slices verify in seconds. This precision motivates real work, cutting anti-spam overhead while preserving user privacy. zkverifiedtasks. com thrives here, turning slow verifies into instant rewards.
DSperse Framework: Slicing for Distributed Bounty Power
Launched in August 2025, DSperse redefines model slicing zk bounties with its modular approach to distributed ML inference. It carves the pipeline into verifiable "slices, " targeting subcomputations for zk proofs without full circuitization. Provers handle slices independently, slashing overhead by orders of magnitude. For bounties, this means verifying task completions across decentralized networks without trusting anyone.
DSperse's genius lies in strategic verification: prove high-risk slices deeply, skim low-risk ones. Tailored for Web3, it supports diverse deployments, from on-chain bounties to off-chain oracles. Bounty platforms gain cryptographic integrity minus the bloat, empowering developers to innovate fearlessly.
TeleSparse Takes Slicing to Transformer Heights
April 2025 brought TeleSparse, a beast for proving modern nets like transformers and vision models. It sparsifies activations post-processing, teleporting neural values to optimal ranges, gutting circuit constraints. Prover memory drops 80%, times halve, accuracy barely blinks. For fast bounty proof generation, it's gold: slice a bounty's vision task, prove slices in parallel, claim rewards pronto.
Combine with ZKLoRA from January 2025, verifying LoRA adaptations sans base model leaks. Multi-party inference ensures collaborative bounties stay secure. These tools stack, building robust distributed zk proofs tasks ecosystems. zkverifiedtasks. com integrates similar slicing, motivating hunters with reliable, rapid payouts.
ZKLoRA's Multi-Party Inference shines in bounty scenarios where teams collaborate on model tweaks without spilling secrets. Slice the LoRA module, prove its merge with the base model via succinct proofs, and verify task outputs deterministically. Latency plummets, making it ideal for real-time Web3 bounties. I've seen similar modular strategies in trading: adapt indicators swiftly, confirm with volume, and execute. Here, slicing delivers that same crisp edge for model slicing zk bounties.
ZKLoRA Protocol: Secure LoRA Slicing for Collaborative Tasks
January 2025's ZKLoRA tackles untrusted training head-on, ensuring LoRA weights play nice with base models. By slicing adaptations into verifiable chunks, it enables decentralized bounty hunters to contribute without exposing IP. The protocol's low-latency checks fit high-throughput platforms perfectly, where every second counts toward rewards. Pair it with DSperse's distribution, and you've engineered a powerhouse for distributed zk proofs tasks.
Comparison of DSperse, TeleSparse, ZKLoRA
| Framework | Key Technique | Prover Speed Gain | Bounty Use Case | Memory Reduction |
|---|---|---|---|---|
| DSperse | Targeted verification of specific subcomputations ("slices") | Reduced computational overhead for full-model circuitization | Scalable verification of bounty submissions in distributed ML inference | Lower overhead compared to full-model circuitization |
| TeleSparse | Sparsification and neural teleportation for activation optimization | Significant decrease in proof generation time | Efficient ZK proofs for large models (e.g., transformers) in bounty verification | Decreased prover memory usage |
| ZKLoRA | Succinct proofs and Multi-Party Inference for LoRA modules | Low-latency verification | Secure LoRA compatibility checks in decentralized bounty programs | Optimized for untrusted environments |
These frameworks aren't silver bullets alone; their real magic emerges in combination. Stack TeleSparse's sparsification on DSperse slices, layer ZKLoRA for adaptations, and bounty verification becomes a breeze. At zkverifiedtasks. com, we prioritize such hybrids to deliver efficient zkML verification, letting developers focus on creation over computation woes.
Hands-On: Slicing Your First Bounty Proof
Ready to slice like a pro? Start small: pick a bounty task with a sliced CNN layer. Convert to Circom, enforce activations within bounds, and generate per-slice proofs. Parallelize across GPUs, recurse aggregates, submit to the chain. This workflow crushes traditional proofs, motivating consistent bounty hunting. It's practical power: verify fast, earn faster.
Challenges persist, sure, optimizing slice boundaries demands care, and recursion adds minor overhead. Yet, the upsides dominate: scalability for massive models, privacy for sensitive bounties, and motivation through swift rewards. Swing traders thrive on momentum; zk verifiers now ride slicing's wave.
As Web3 bounties explode, model slicing cements its role in fast bounty proof generation. DSperse distributes the load, TeleSparse slims the circuits, ZKLoRA secures collaborations. zkverifiedtasks. com stands at the forefront, blending these for seamless, fraud-proof verification. Dive in, slice smart, and claim your edge in the decentralized frontier.






No comments yet. Be the first to share your thoughts!