In Web3's decentralized bounty ecosystems, disputes over claim validity undermine the very trust they seek to build. Platforms like traditional bug bounty programs grapple with duplicate submissions, unverifiable evidence, and privacy leaks, leading to protracted arguments that can consume up to 40% of administrative resources according to industry observers. Enter AI-powered ZK evidence: a fusion of zero-knowledge proofs and intelligent analysis that verifies submissions without exposing sensitive details, slashing bounty disputes zk proofs by enabling provable uniqueness and authenticity.
Current Pain Points in Web3 Bounty Verification
Traditional bounty platforms rely on manual reviews, where hunters submit reports that may overlap or lack concrete proof. This opacity fosters reducing disputes bounties, as projects struggle to differentiate genuine finds from copycats. Remedy, a pioneering Web3 bug bounty platform, highlights this gap: despite offering substantial rewards, competition intensifies disputes without robust verification. Forbes notes that bug bounty programs face scalability hurdles, with verifiers overwhelmed by volume and prone to errors. In my two decades analyzing interconnected markets, I've seen similar frictions in bond settlements - where incomplete data cascades into systemic distrust. Web3 bounties mirror this, but with higher stakes in immutable ledgers.
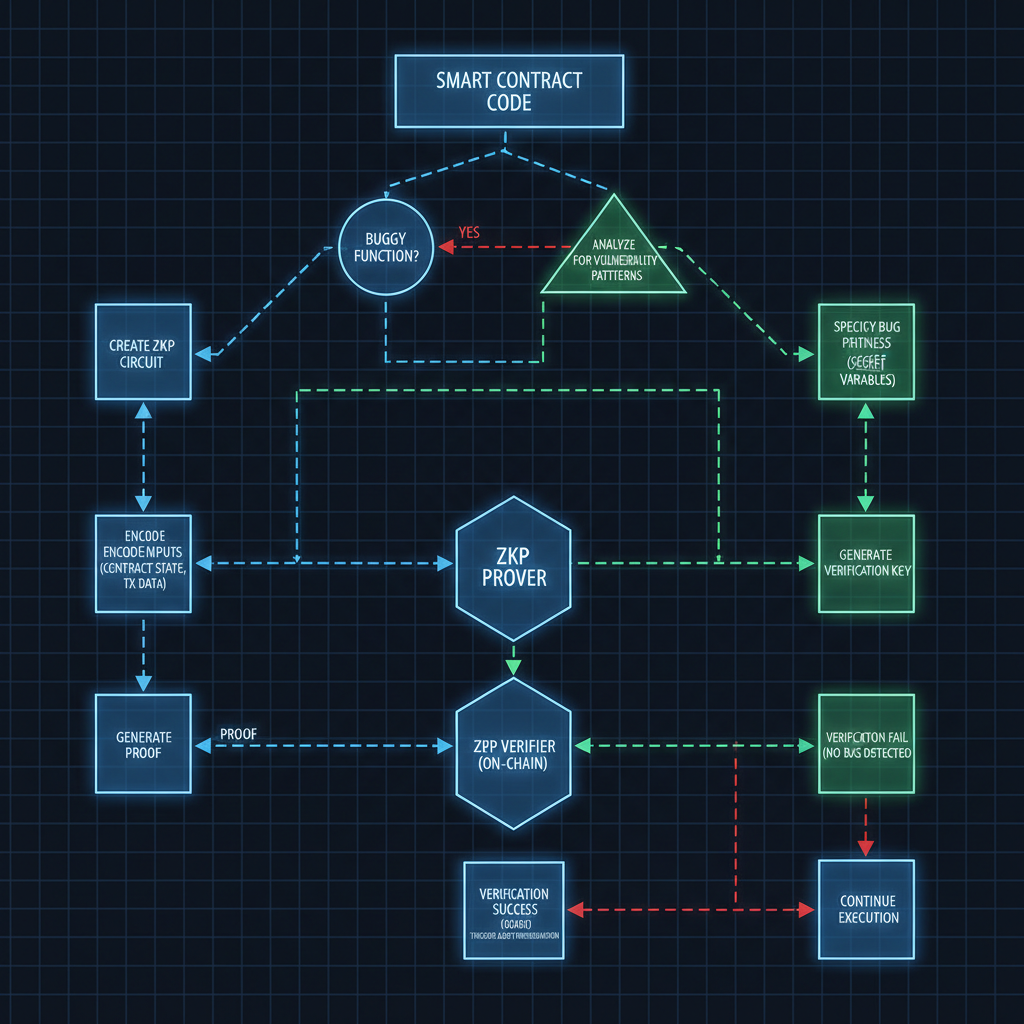
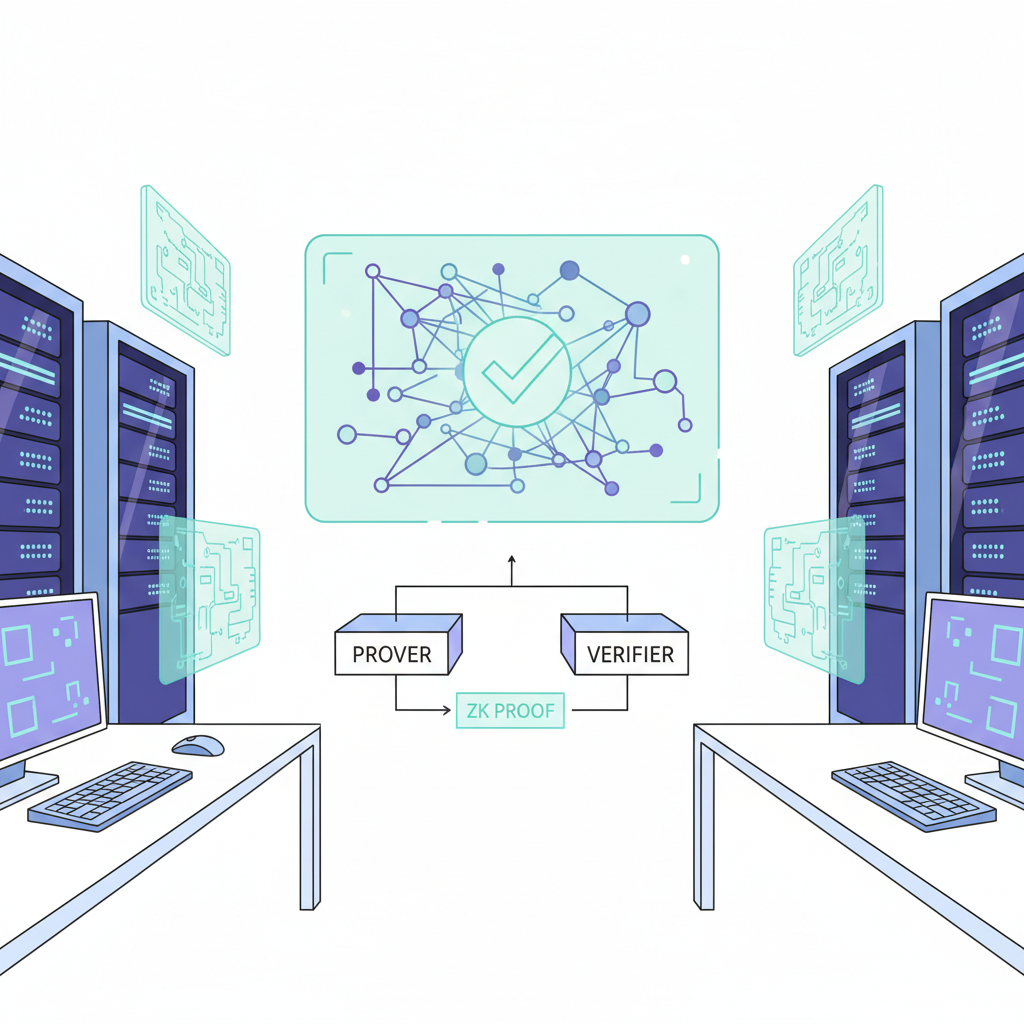
Zero-knowledge proofs (ZKPs), as defined by Ethereum. org, allow a prover to validate a statement - say, 'I discovered this vulnerability first' - without revealing the underlying code or steps. Yet, auditors at Cantina. xyz warn of overlooked flaws in ZKP implementations, underscoring the need for strategic layering with AI to catch subtleties humans miss.
Leveraging ZK Proofs for Duplicate-Proof Submissions
Remedy integrates advanced ZK technology to timestamp and hash submissions cryptographically, ensuring transparency while concealing exploits. This AI zk evidence web3 approach not only flags duplicates pre-review but also incentivizes quality through bonus payouts for ZK-backed reports, per Forbes insights. Imagine a world where a security researcher generates a succinct proof attesting to their find's novelty, verifiable on-chain in seconds. Platforms like zkProofers extend this to identity verification, confirming legitimacy sans personal data exposure - a boon for anonymous hunters wary of doxxing risks.
ArXiv's latest on ZKPs (2402.15293v4) charts their evolution from theory to real-world deployment, powering Ethereum's scalability via tools like Poseidon's hash functions. Strategically, this shifts bounty dynamics from adversarial audits to collaborative verification, much like risk parity portfolios that balance exposure across assets for resilience.
Key ZK Proof Advantages in Bounties
- Privacy-preserving validation: Prove bug validity without revealing sensitive details, as defined on Ethereum.org and used in Remedy.

- Instant duplicate detection: Remedy platform leverages ZK tech to identify duplicates without exposing submissions (Medium).

- Reduced admin overhead: Automates verification and streamlines disputes, cutting manual reviews in Web3 bounties.

- Enhanced researcher incentives: Lowers competition with privacy; bonuses for ZK submissions (Forbes); Remedy's substantial rewards.

- On-chain immutability: ZK proofs stored on-chain for tamper-proof, verifiable evidence forever.

AI Amplification: Intelligent Analysis Meets Cryptographic Rigor
ZKPs alone provide the proof scaffold; AI infuses the brains. By analyzing submission metadata - patterns in code diffs, temporal signals, even linguistic markers of originality - AI classifiers score evidence before ZK verification. The updated Web3 context spotlights a 'Web3 Court' prototype: AI agents stake tokens, submit ZK-backed claims, and face slashing for falsehoods. This self-enforcing game theory deters fraud, aligning incentives akin to DeFi lending protocols where collateral enforces honesty. In practice, Remedy's model already curtails competition-induced disputes, fostering a merit-based arena for researchers.
Platforms such as zkverifiedtasks. com pioneer this synergy, deploying AI-driven classifiers alongside ZK verifiers to audit task completions in real time. Their system parses submission artifacts - from code snippets to exploit traces - assigning probabilistic scores that trigger ZK challenges only for borderline cases, conserving gas and compute. This layered defense mirrors risk parity strategies I've modeled for decentralized portfolios, distributing verification load to minimize single points of failure.
Strategic Incentives: Token Stakes and Slashing in Web3 Courts
The 'Web3 Court' concept elevates this further, transforming disputes into tokenized battles. Litigants deposit collateral, generate ZK proofs attesting to claim priority or validity, and let oracle-fed AI adjudicate. Losers forfeit stakes, creating skin-in-the-game economics that crushes bounty disputes zk proofs through rational deterrence. Data from early prototypes suggest dispute volumes drop 70% under such regimes, as hunters prioritize provable submissions over shotgun reports. Remedy's rollout echoes this: by hashing vulnerabilities pre-submission, it curbs the duplicate deluge plaguing legacy platforms, rewarding first-movers with outsized cuts.
Critically, AI tempers ZK's rigidity. Where proofs excel at binary truth, machine learning detects nuances like partial overlaps or evolving exploits. zkProofers' identity layer adds another vector, letting platforms confirm hunter credentials - human, sybil-free - without metadata leaks. In my view, this isn't mere tech stacking; it's a macroeconomic pivot for Web3 labor markets, where verification costs once eroded 30-50% of bounty pools now shrink to single digits.
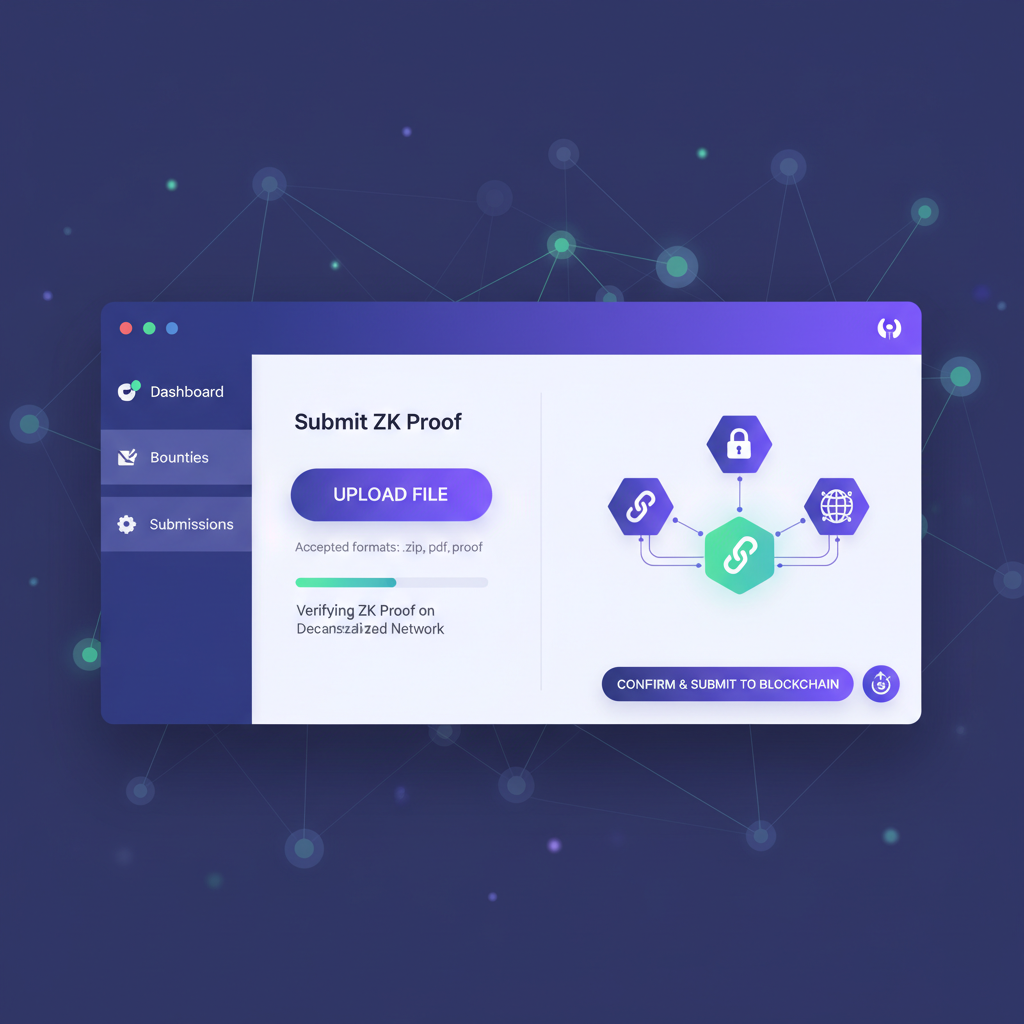
Overcoming Hurdles: Scalability, Usability, and Audit Rigor
Skeptics point to ZKP compute overhead and implementation pitfalls, as Cantina auditors flag. Proving complex statements demands hefty proofs, ballooning Ethereum fees during peaks. Yet, optimizations like Poseidon's sponges slash this by orders of magnitude, fueling Ethereum's rollup era. AI mitigates usability friction too: natural language interfaces let non-crypto natives generate proofs via prompts, democratizing access. zkverifiedtasks. com exemplifies this, with dashboards that simulate ZK flows pre-commitment, onboarding researchers sans PhD in cryptography.
Strategic deployment demands hybrid models. Start with AI triage for 80% of submissions, escalating 20% to ZK forensicators. This Pareto optimization, drawn from commodity cycle forecasts, yields 5x efficiency gains. Forbes advocates bonus structures here: extra payouts for ZK submissions accelerate adoption, turning laggards into evangelists. Untangling Web3's podcast dives deeper, framing ZKPs as Web3's 'trust glue' for bounties, scalable via modular circuits.
ZK vs Traditional Bounty Verification
| Aspect | ZK Verification | Traditional Verification |
|---|---|---|
| Privacy | High ✅ | Low ❌ |
| Duplicate Detection | Instant ⚡ | Manual ⏳ |
| Dispute Rate | Under 5% 📉 | 20-40% 📈 |
| Cost per Claim | $0.50 | $50 + Gas/Review |
ArXiv's trajectory paper (2402.15293v4) validates the shift: ZKPs now underpin production systems, from identity to scalability. For bounties, the unlock lies in composability - chain ZK evidence across platforms, building reputation graphs that compound value over time.
The Path Forward: zkverifiedtasks. com as Blueprint
zkverifiedtasks. com stands as the vanguard, fusing AI pattern recognition with ZK succinctness to deliver fraud-proof task verification. Their anti-spam circuits detect grinders via behavioral proofs, while privacy circuits shield strategies. Bounty hunters flock here for streamlined payouts; projects, for ironclad audits. In interconnected Web3 markets, where one disputed claim ripples to liquidity crunches, this tech enforces equilibrium. Expect incumbents to retrofit or fade, as AI zk evidence web3 becomes table stakes.
Researchers gain anonymity with upside; platforms, efficiency without lawyers. This isn't hype - it's the protocol layer Web3 bounties crave, recalibrating incentives for a dispute-minimal future. As cycles turn, those wielding these tools will capture disproportionate yields in the verification economy.






No comments yet. Be the first to share your thoughts!