In the bustling ecosystem of Web3 bounties, where developers and hunters chase rewards for solving complex tasks, fraud lurks as a persistent shadow. Submissions riddled with spam, fabricated proofs, or plagiarized code undermine trust and drain resources. Enter the fusion of artificial intelligence and zero-knowledge proofs: a duo revolutionizing secure bounty verification. Platforms like zkverifiedtasks. com lead this charge, leveraging AI-driven analysis with cryptographic ZK proofs to confirm task completions privately and indisputably. This isn't just tech hype; it's a practical shield against the vulnerabilities plaguing bounty platforms today.
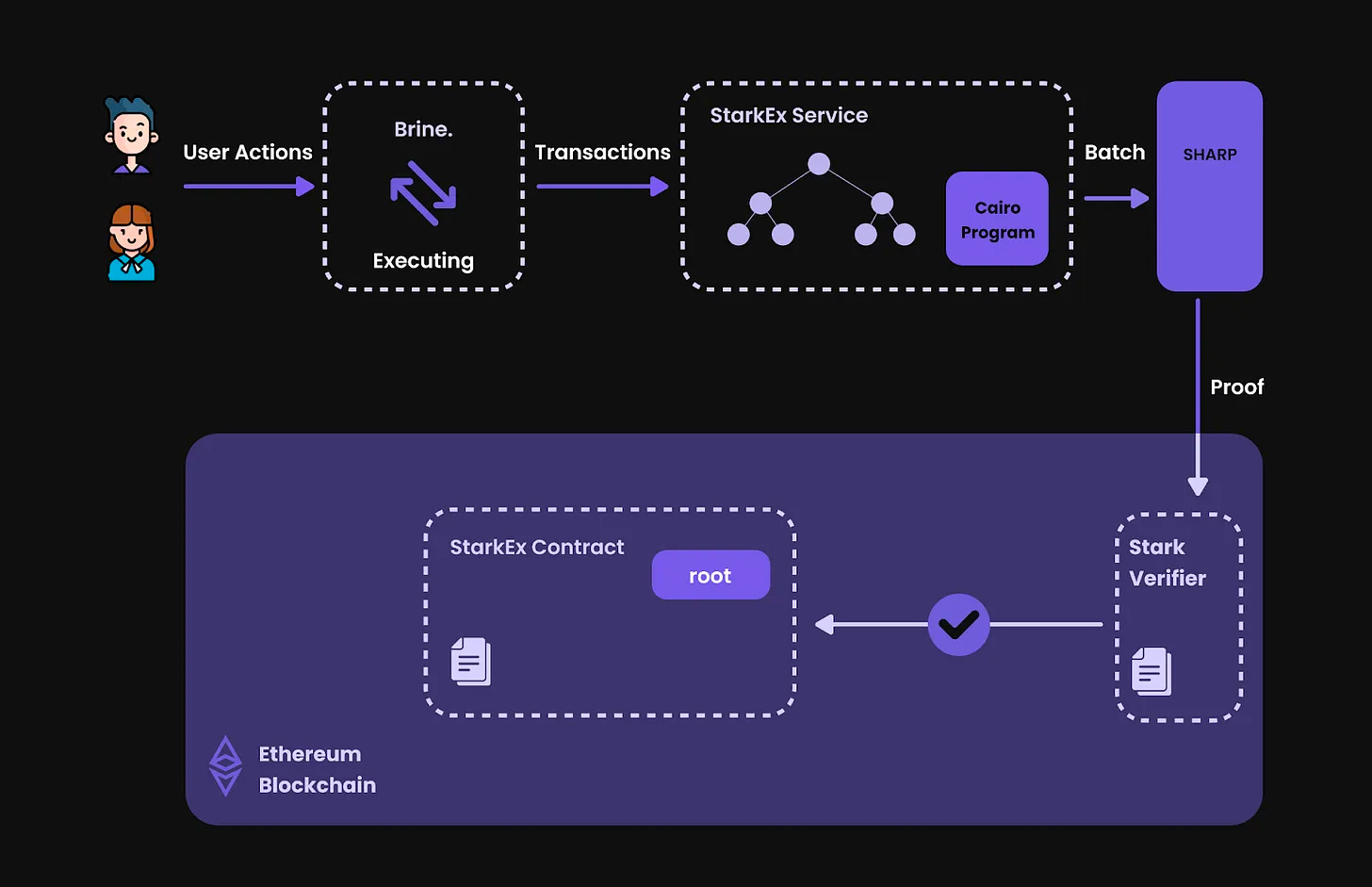
Consider the scale: decentralized projects post bounties for bug hunts, content creation, or protocol audits, only to sift through noisy submissions manually. Traditional checks expose sensitive data, invite disputes, and favor insiders. AI steps in first, parsing code, validating logic, and flagging anomalies with precision honed from vast datasets. Yet AI alone risks opacity; enter ZK proofs, which mathematically attest to correctness without revealing inputs. As highlighted in HKDCA's report on Web3 and AI, ZKML enables audits sans data exposure, a perfect fit for AI task verification in Web3.
Unmasking Fraud in Bounty Ecosystems
Fraud prevention in Web3 bounties demands more than vigilance; it requires systemic redesign. Bounty hunters might submit doctored screenshots or AI-generated facsimiles of work, evading basic checks. Platforms suffer from sybil attacks, where one actor floods with fake identities. Sources like Block Trix emphasize how ZKPs thwart such deception by ensuring provers can't falsify claims. In practice, this means a hunter proves task completion - say, finding a smart contract vulnerability - via a succinct proof, verifiable on-chain without exposing the exploit details.
Key AI + ZK Benefits for Web3 Bounties
- Privacy Preservation: ZK proofs enable verification of bounty submissions without exposing sensitive data, as in BlockBounty for ethical hackers.

- Anti-Spam Filtering: AI detects fraudulent or spam submissions, combined with ZK for private, auditable checks per HKDCA and Extrimian solutions.

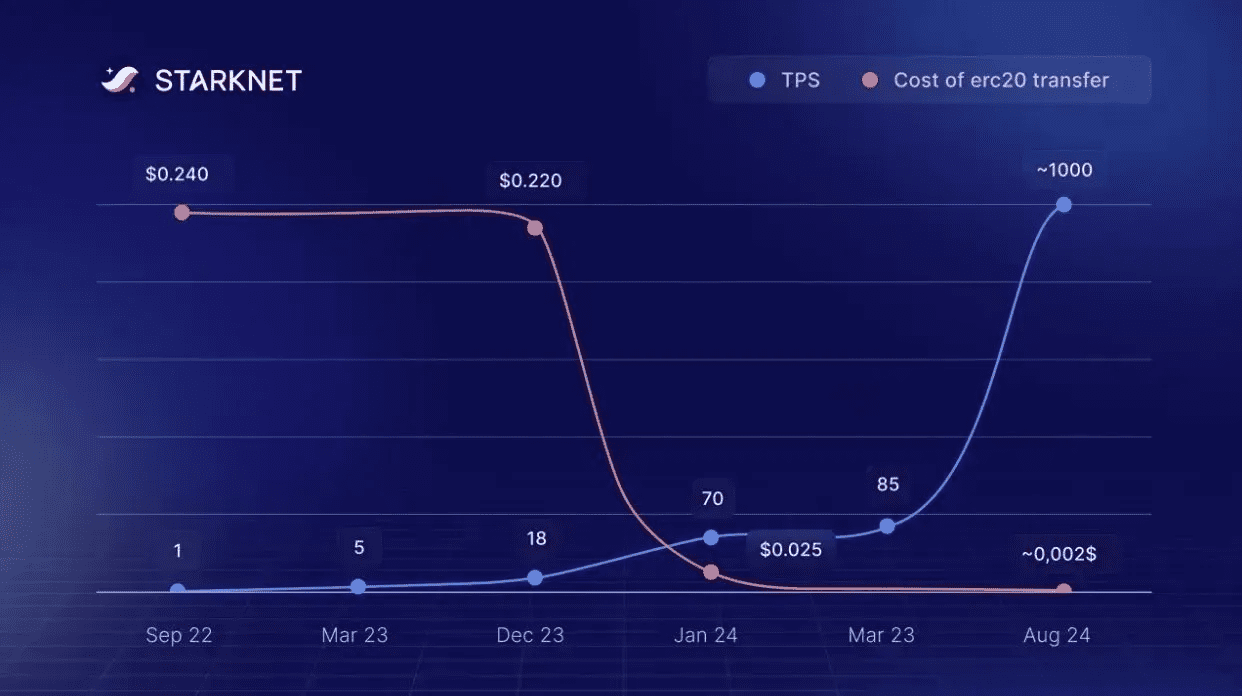
- Scalable Verification: zkVerify mainnet supports multiple proof systems for efficient, cross-chain attestations at scale.
- Cost Reduction: Dedicated ZK infrastructure like zkVerify lowers verification expenses for high-volume Web3 bounties.
- Trustless Rewards: On-chain ZK attestations ensure automatic, fraud-proof payouts without intermediaries.

Take BlockBounty as a real-world parallel: ethical hackers submit vulnerabilities under ZK wraps, verified on-chain privately. This model scales to general bounties, where AI pre-screens for relevance before ZK finalizes integrity. Codezeros notes ZK's role in keeping AI-driven fraud detection both private and auditable, echoing Intellectia AI's take on zk-SNARKs for secure computation in detection and reviews.
AI's Role in Intelligent Submission Scrutiny
Artificial intelligence transforms raw submissions into actionable insights. Machine learning models trained on historical bounty data detect patterns of deceit: inconsistent code styles, unnatural language in reports, or mismatched timestamps. For zk proofs Web3 bounties, AI doesn't just classify; it simulates task execution in sandboxes, comparing outputs against expected results. Extrimian's AI-SSI stack, for instance, slashes fraud across industries, a blueprint for bounties.
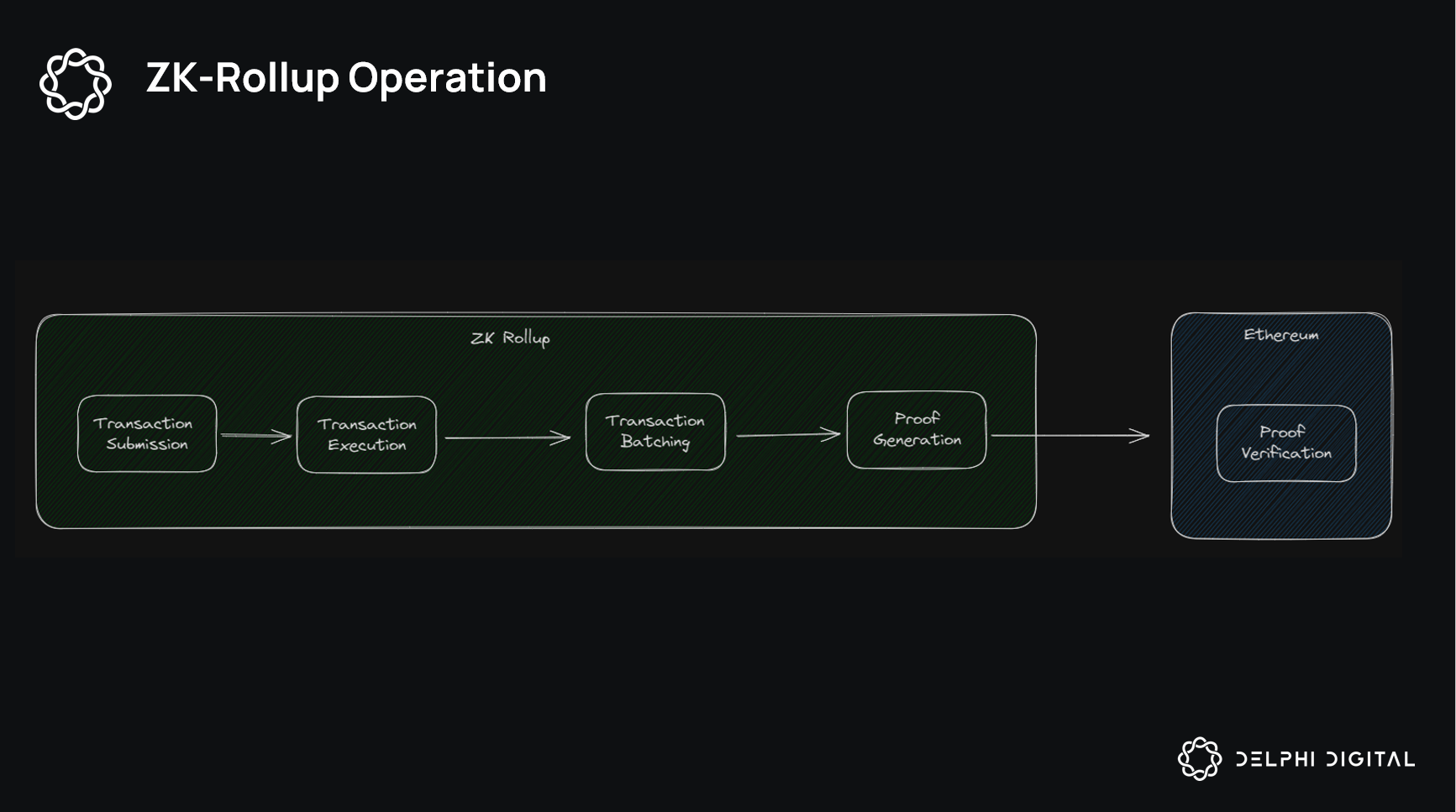
Yet AI's strength lies in augmentation, not isolation. Optimistic verification, as ChainScore Labs describes, pairs AI with fraud proofs; if challenged, ZK resolves disputes definitively. This hybrid catches 99% of fraud upfront, reserving heavy crypto for edge cases. zkVerify's mainnet launch amplifies this, offering cheap, multi-proof verification attestations cross-chain, slashing costs for bounty platforms.
ZK Proofs: Cryptographic Backbone for Trustless Verification
Zero-knowledge proofs shine in their elegance: prove knowledge of a solution without disclosure. In bounties, a prover generates a zk-SNARK attesting 'I completed the task correctly' relative to public criteria. Verifiers check in milliseconds, no oracle needed. Humanity Protocol's zkProofers extend this to identity, eliminating sybil fraud in bounty claims.
Arguzz's zkVM testing reveals the rigor behind reliable ZK systems, catching soundness bugs early. BNB Chain's fraud proof mechanics in L2s inspire similar on-chain checks for bounties. Proof. com's Certify merges ZK with AI for notarization, a harbinger for bounty attestations. Fintech Nexus' Ezekiel builds trusted AI atop ZK, ensuring verifications withstand scrutiny.
This synergy isn't theoretical. Bounty platforms integrating AI for triage and ZK for proof craft fraud prevention Web3 bounties ecosystems where rewards flow swiftly to legitimate contributors, fostering innovation sans fear.
At zkverifiedtasks. com, this vision materializes through a streamlined pipeline tailored for Web3 bounties. Developers post tasks with clear criteria, hunters submit work, and our AI engine dissects it layer by layer: semantic analysis of code, behavioral scoring of reports, even cross-referencing with on-chain activity. Suspicious entries get flagged, while promising ones trigger ZK proof generation, where hunters attest to compliance without baring their methods. Verifiers - project leads or decentralized committees - confirm in seconds, releasing funds trustlessly. This setup not only curbs fraud prevention Web3 bounties but elevates the entire hunter economy, rewarding skill over sleight of hand.
Scaling Verification: From Edge Cases to Ecosystem Standard
Scalability defines the next frontier. Traditional bounty verification buckles under volume; manual reviews lag, costs balloon. zkVerify's mainnet changes that calculus, hosting proofs cheaply across systems like Groth16 or Plonk, issuing portable attestations for any chain. Imagine a bounty for DeFi protocol hardening: AI triages 1,000 submissions to 50 finalists, ZK proves their fixes patch vulnerabilities correctly. No data leaks, no disputes, just payouts. Arguzz's zkVM audits underscore why this reliability matters; overlooked bugs could unravel proofs, but rigorous testing fortifies the stack.
Proof of Useful Work, as ChainScore Labs outlines, extends this to AI tasks themselves - bounties for model training or inference, verified via zk-SNARKs or lighter fraud-proof hybrids. BNB Chain's L2 fraud proofs offer a blueprint: publish commitments, challenge invalid ones, settle with crypto math. Humanity Protocol's zkProofers layer identity atop this, sybil-proofing claims so one wallet can't dominate leaderboards. Extrimian's fraud reductions via AI-SSI hint at broader applications, from gaming bounties to DAO proposals.
Critics might balk at ZK's computational heft, but maturing tools like Ezekiel from Fintech Nexus embed it seamlessly into AI workflows, building verifiable intelligence from the ground up. Platforms adopting this hybrid outpace rivals; zkverifiedtasks. com exemplifies how zero knowledge proofs bounties become the norm, not the exception.
Real-World Impact and Future Horizons
BlockBounty's vulnerability disclosures prove the model's mettle: hackers earn without tipping exploits prematurely, projects patch swiftly. zkverifiedtasks. com amplifies this for all tasks - audits, content, integrations - weaving AI's nuance with ZK's rigor. Fraud drops precipitously; one study analog from Proof. com's Certify shows notarization slashing disputes by orders of magnitude. Hunters gain confidence, projects save time, ecosystems thrive.
Looking ahead, expect ZKML to evolve AI verifiers themselves, proving model decisions privately. Onboarding via ZK-AI, as Codezeros envisions, secures bounty participation from the start. Intellectia AI's secure computation for reviews points to contract bounties verified end-to-end. This isn't incremental; it's a paradigm shift toward AI task verification Web3 where privacy fuels participation, not paranoia.
Bounty platforms ignoring this convergence risk obsolescence. Those embracing it, like zkverifiedtasks. com, forge ahead: tamper-proof, efficient, inclusive. In Web3's meritocracy, where code is king, secure bounty verification ensures the crown goes to the worthy.









No comments yet. Be the first to share your thoughts!