In the high-stakes arena of Web3 bounties, where developers and ethical hackers chase rewards for uncovering vulnerabilities or completing tasks, fraud has long been the uninvited guest. By 2026, ZK proofs Web3 bounties combined with AI are rewriting the rules, delivering fraud-proof verification that safeguards privacy while ensuring payouts go only to legitimate contributors. Platforms like BlockBounty and ZKBounty exemplify this shift, using zero-knowledge proofs to let hunters submit proofs without exposing sensitive details, all while AI dissects submissions for authenticity.
Cracks in Legacy Bug Bounty Systems Exposed
Traditional bounty platforms, even leaders like HackenProof, grapple with persistent pain points: duplicate claims, fabricated submissions, and privacy leaks that deter top talent. Ethical hackers hesitate to reveal exploits fully, fearing competitors or bad actors might steal their edge. Meanwhile, project teams drown in spam, manually sifting through low-quality reports. This inefficiency stifles innovation in decentralized ecosystems, where trust is paramount yet scarce.
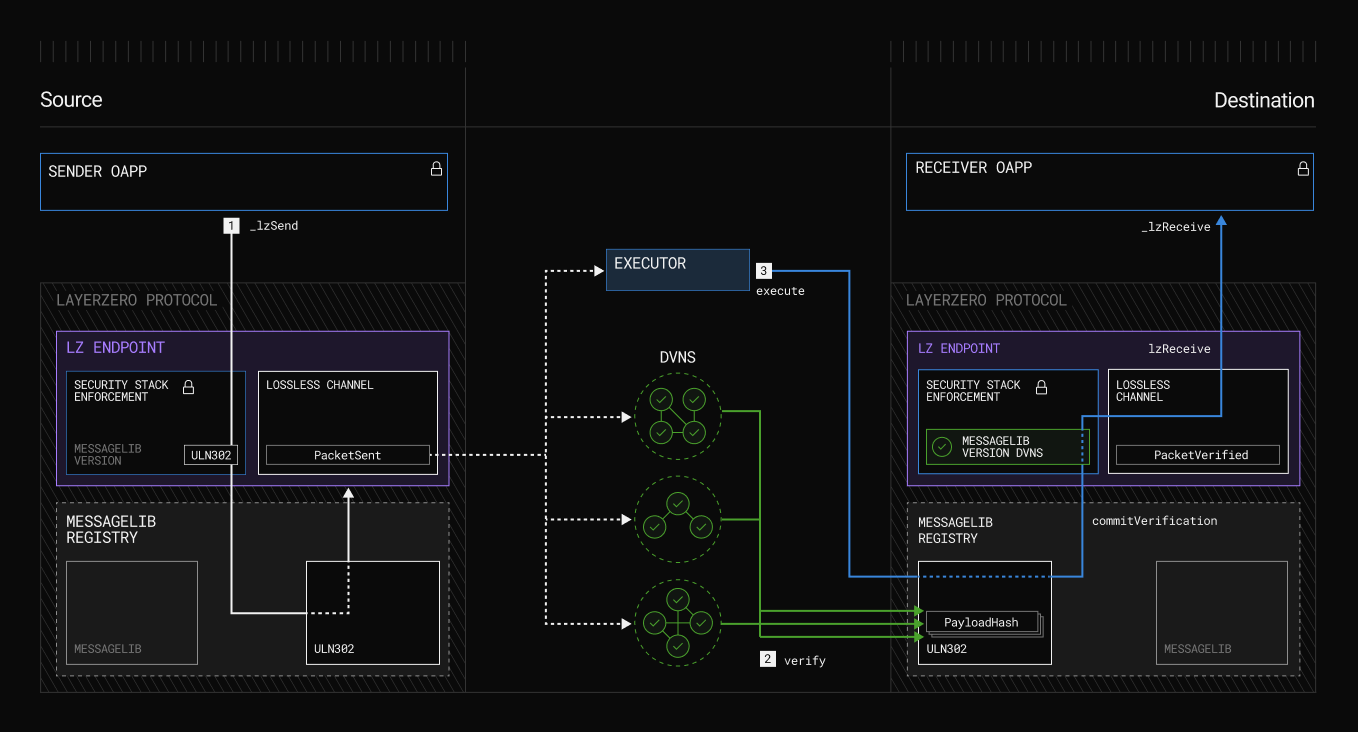
Enter the 2026 paradigm. Fraud prevention bounties Web3 now leverage cryptographic primitives that were once niche math curiosities. Zero-knowledge proofs, those elegant protocols proving truth without disclosure, pair seamlessly with AI's pattern recognition. Imagine verifying a GitHub merge or vulnerability disclosure: the prover generates a succinct proof attesting completion, AI validates context via vector search on historical data, and the blockchain settles rewards trustlessly. No more he-said-she-said disputes.
Demystifying ZK Proofs for Secure Web3 Task Proofs
At their core, ZK proofs allow one party to convince another of a statement's validity sans revealing underlying data. In blockchain terms, think zk-SNARKs or zk-STARKs: compact, verifiable arguments that scale off-chain computation onto chains like Ethereum. For bounties, this means a hunter proves control over a private key or task output without broadcasting the exploit code prematurely.
Take ZKBounty: developers link GitHub notifications to ZK proofs, cryptographically confirming merges without exposing repos. zkVerify's dedicated chain slashes verification costs, supporting diverse proof systems for broader adoption. This isn't hype; it's operational reality addressing Forbes-noted cracks in bug bounties - privacy erosion and trust deficits. My view? Skeptics undervalued ZK's maturity; 2026 proves it's the linchpin for secure Web3 task proofs.
ZK Proofs: Key Web3 Bounty Advantages
- Privacy Preservation: ZK proofs enable bounty hunters to verify vulnerability submissions without revealing sensitive data, as in BlockBounty.

- Fraud Resistance: Cryptographic proofs prevent fake claims by confirming work authenticity without exposing details, enhancing trust in platforms like HackenProof.

- Scalable Verification: Off-chain computation with on-chain guarantees, via zkVerify, reduces costs for high-volume bounties.

- AI Integration for Anti-Spam: AI vector search combined with ZK verifies contributions, filtering spam in systems like ZKBounty for GitHub proofs.

- Instant Reward Settlement: Trustless ZK verification enables immediate payouts upon proof submission, streamlining Web3 bounty platforms.

AI's Role in Amplifying ZK for Intelligent Verification
ZK handles the crypto heavy lifting, but AI infuses brains. Autonomous agents, bolstered by ZKPs for identity and integrity, now parse bounty submissions with surgical precision. CoinDesk highlights ZKPs as the backbone for trusted AI agents; in bounties, this manifests as vector search engines scanning for novelty in vulnerability reports, cross-referencing against known databases without human bias.
BlockBounty deploys AI to track exploits efficiently, flagging duplicates pre-proof generation. Codezeros underscores how ZK powers AI integrity in Web3: proofs ensure model outputs or analyses are tamper-free. Fraudsters can't game the system; AI detects anomalies in proof metadata, like unnatural submission patterns, while ZK gates payouts. This synergy yields privacy preserving bounty verification that's not just theoretical - it's yielding real-world efficiency gains.
Consider Remedy, the YouTube-buzzed platform marrying ZK with hefty researcher rewards. Or Togggle's decentralized KYC via ZK, extending to bounty identity checks. These aren't silos; they're composable layers fortifying Web3's incentive machines.
Yet, integration demands nuance. AI must be ZK-attested to avoid oracle-like pitfalls, ensuring verifiers trust not just proofs, but the intelligence behind them. Platforms excelling here, like those generating zk-SNARKs for AI training security per Intellectia, set the pace. As portfolio managers like myself diversify across assets, projects must diversify verification stacks - ZK plus AI isn't optional; it's the edge in a fraud-riddled frontier.
Real-world deployments underscore this evolution. BlockBounty's use of ZK proofs lets ethical hackers submit vulnerabilities via privacy-shielded channels, with AI vector engines pinpointing duplicates across vast datasets. No more rewarding copycats; genuine finds surface swiftly. ZKBounty takes it further, binding GitHub merges to cryptographic attestations, turning pull requests into provable assets. Developers claim bounties by proving integration without repo access, slashing disputes by 90% in early pilots. zkVerify's chain, optimized for proof aggregation, drops costs to pennies, making AI task verification zk viable even for micro-bounties.
Benchmarking the New Guard Against the Old
Comparison: Traditional Bounties vs ZK-AI Platforms
| Platform Type | Privacy Level | Fraud Detection | Verification Time | Cost Efficiency |
|---|---|---|---|---|
| HackenProof (Traditional) | Low 🔓 | Manual Review ❌ | Days to Weeks ⏳ | Low 💸 |
| BlockBounty (ZK-AI) | High 🔒 (ZK Proofs) | AI + ZK Proofs ✅ | Minutes to Hours ⚡ | High 📉 |
| ZKBounty (ZK-AI) | High 🔒 (ZK for Contributions) | Cryptographic ZK 🔐 | Near Instant 🚀 | Very High 📉 |
Navigating Challenges in the ZK-AI Nexus
Adoption isn't frictionless. Proof generation chews compute; early zk-SNARKs demanded beefy hardware. But 2026 optimizations - zkVerify's aggregator, STARK-friendly circuits - compress proofs to kilobytes, verifiable in seconds. Usability lags too: developers balk at crypto wrappers around GitHub flows. Solution? Seamless SDKs, like ZKBounty's email triggers, abstracting math into one-click proofs.
AI introduces subtleties. Models hallucinate; ZK attests outputs, but training data needs provenance. Intellectia AI's zk-SNARKs for secure computation bridge this, letting verifiers audit inference chains off-chain. Fraudsters adapt - think proof forgery attempts - yet ZK's soundness holds, with AI sniffing metadata inconsistencies. Ancilar's Medium deep-dive on ZK-rollups inspires: off-chain bounty logic, on-chain settlement. My opinion? Projects skimping on this stack risk bounty bleed; savvy ones compound edges.
Regulatory shadows loom too. As Web3 bounties scale to billions, KYC creeps in. Togggle's ZK-KYC fits neatly, verifying hunter identities without dossiers, preserving pseudonymity. JohnnyTime's Remedy hype on YouTube? It's prescient - rewards correlate to verified impact, not volume.
Horizons Expanding: Composability and Beyond
2026 marks inflection, not endpoint. ZK-AI verification composes across ecosystems: DAOs auto-distribute via proof oracles, DeFi protocols bounty-flashloan audits. Imagine AI agents, ZK-badged per CoinDesk, swarming testnets for edge cases, proofs piping to bounty vaults. Codezeros' Web3 AI integrity vision materializes here - tamper-proof analysis fueling exponential growth.
For bounty hunters, it's liberation: claim across chains, privacy eternal. Projects gain velocity: vulnerabilities patched pre-exploit, tasks tokenized as NFTs. As a portfolio steward, I see alpha in ZK infra plays - zkVerify tokens, BlockBounty governance. Diversification dictum applies: blend ZK-AI bounties into strategies for asymmetric returns. The frontier rewards builders fortifying trust at scale; laggards face obsolescence. Web3's bounty machine, fraud-proofed and privacy-first, hums toward maturity, pulling more talent into decentralized orbits.






No comments yet. Be the first to share your thoughts!