In the high-stakes arena of Web3 bounty programs, where millions in crypto rewards hang in the balance, Sybil attacks have become the silent killer of trust. Fast-forward to 2026, and the landscape has shifted dramatically. AI task verification Web3 combined with zero-knowledge proofs delivers unbreakable sybil resistant bounties, slashing fraud while preserving user anonymity. Platforms like zkverifiedtasks. com stand at the forefront, fusing intelligent AI analysis with zk proofs to verify tasks cryptographically, ensuring only real contributors claim bounties. This isn't just tech hype; it's a practical revolution for developers and hunters chasing legitimate payouts amid rampant bot swarms.
AI's Precision Strike Against Automated Fraud
Picture this: a bounty hunter submits a critical smart contract audit, only for a horde of AI-generated Sybil identities to flood the system with bogus claims. Traditional CAPTCHAs crumbled years ago under sophisticated bots. Enter AI-driven defenses like the Human Challenge Oracle (HCO), which deploys time-bound puzzles exploiting human strengths in perception and reasoning. Humans solve them in seconds; bots falter under the clock. From my vantage as a portfolio manager navigating crypto volatility, this approach flips the economics: sustaining fake identities now drains adversaries' resources exponentially.
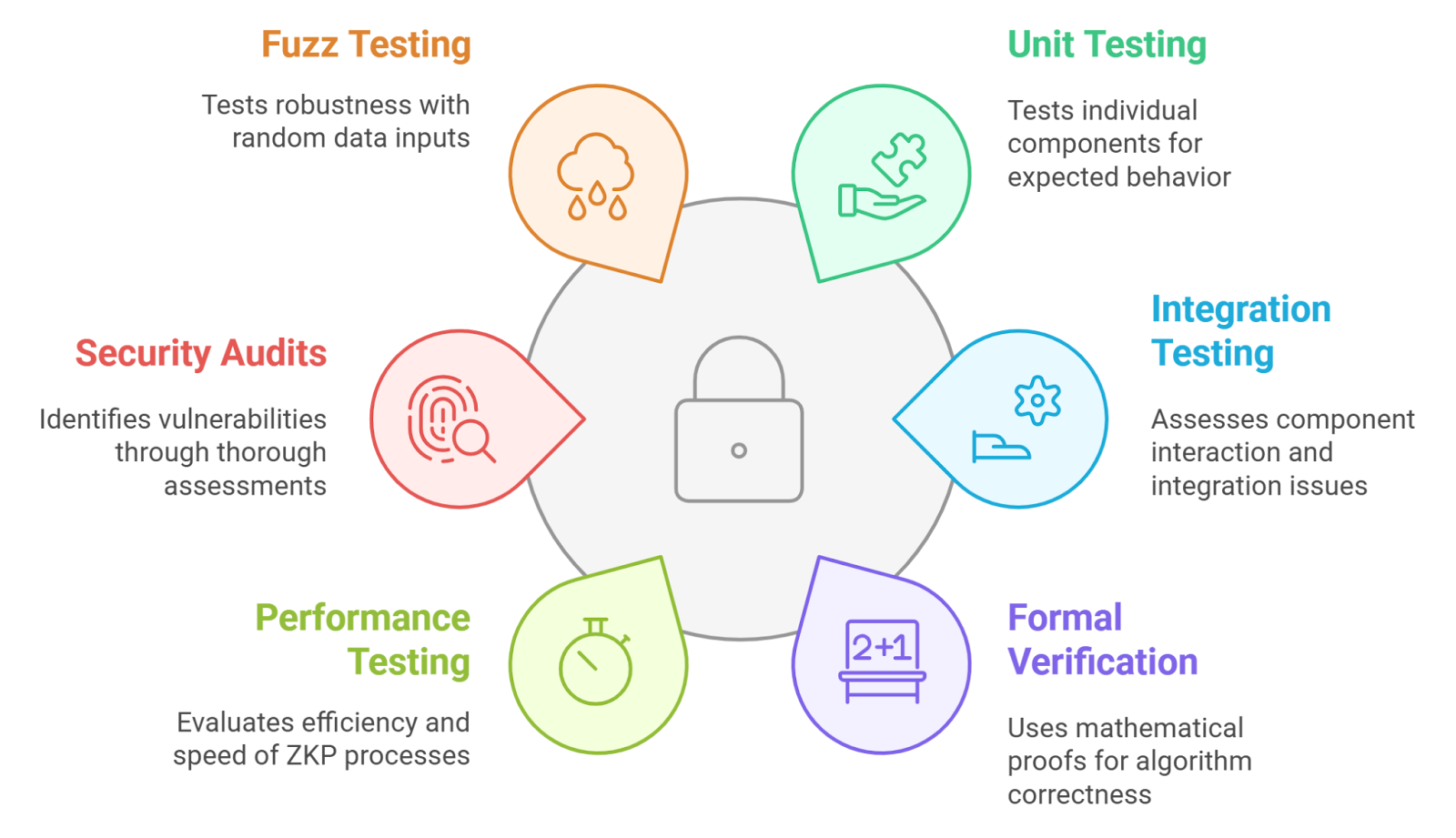
These systems don't just detect; they adapt. Machine learning models evolve with attack patterns, making Web3 bounty anti-spam proactive rather than reactive. zkVerify's toolkit, optimized for scale, verifies AI inferences themselves, proving model integrity without exposing data. It's a layered bulwark, where AI not only guards entry but audits the work, curbing fraud proof bounties zk vulnerabilities that plague platforms like HackenProof and Hashlock.
Key AI Sybil Resistance Advantages
- Human-Centric Challenges: Systems like the Human Challenge Oracle (HCO) deploy time-bound tasks leveraging human cognition, solvable in seconds by people but tough for bots. Source

- Adaptive Bot Detection: AI distinguishes humans from bots via sophisticated, evolving algorithms, as in zkVerify's verifiable ML for fraud prevention.
- Cost Barriers for Attackers: Strict time constraints make sustaining fake identities expensive and impractical for Sybil attackers.

- Seamless ZK Proofs Integration: Pairs with ZK proofs for privacy-preserving verification, like Cysic-Billions Network for bot-proof Web3 identity. Source

ZK Proofs: The Privacy Powerhouse for Identity Assurance
Zero-knowledge proofs take verification to another level, letting users prove attributes - like 'I completed this task uniquely' - without doxxing themselves. zkMe's zkKYC exemplifies this, enabling compliant identity checks that sidestep data leaks. In bounty contexts, imagine proving computational effort on a bug find via zkML, without revealing the code. Forbes highlighted how this fixes bug bounties plagued by AI noise; bonus payouts for ZK-backed submissions incentivize quality.
I've long advocated for such mechanisms to bolster Web3 trust, much like quant models underpin my diversified strategies. ZKML bridges AI and blockchain seamlessly, as seen in Cysic's hardware-accelerated collab with Billions Network. Their bot-proof identity layer uses ZK infrastructure to verify humans amid AI agent chaos, directly fortifying bounty platforms against multi-account exploits.
Seamless Fusion Powering Next-Gen Bounty Ecosystems
Where AI spots the fakes, ZK seals the proof. Together, they streamline zk proofs bounty verification, slashing manual reviews and disputes. Platforms like zkverifiedtasks. com exemplify this: AI analyzes submissions, zk proofs confirm authenticity on-chain, all privacy-preserved. arXiv surveys underscore ZK's versatility, from blockchain privacy to task verification, while Delphi Digital spotlights zkVerify's fraud prevention chops across Web2-Web3.
Real-world adoption surges. HackenProof and Hashlock integrate similar tech for crypto bug hunts, offering crowdsourced security with ZK-enhanced submissions. A Medium proposal for 'cryptoeconomic justice' courts even extends this to AI agents proving token spends. In 2026, this hybrid model isn't optional; it's the gold standard, ensuring bounties reward ingenuity, not impersonation.
Developers on these platforms now focus on innovation rather than fraud worries, with verification times dropping from days to minutes. My experience managing crypto portfolios underscores the value: just as diversified strategies mitigate risk, this tech stack diversifies verification layers for ironclad security.
Real-World Wins and Platform Spotlights
Take zkverifiedtasks. com, the leading hub for AI task verification Web3. It deploys AI to dissect submissions for legitimacy, then zk proofs to cryptographically attest completion without privacy trade-offs. Bounty hunters submit audits or content; AI flags anomalies, ZK confirms uniqueness on-chain. No more disputes over fraud proof bounties zk - proofs are tamper-proof and scalable, thanks to zkVerify's optimizations.
HackenProof leads Web3 bug bounties with crowdsourced audits, now ZK-enhanced to reward only verified finds. Hashlock tailors for smart contracts, where ZK proofs validate vulnerability disclosures privately. These aren't silos; they're part of a broader shift. Codezeros details how ZK powers AI integrity, ensuring models don't hallucinate verifications. From my seat watching market cycles, this convergence mirrors quant edges in forex - precise, data-backed, and ahead of the curve.
The arXiv survey on ZK applications nails it: confidential task verification spans bounties seamlessly. Blockchain Council's take on identity validation fits perfectly, making Bitcoin-era tricks obsolete for modern Sybil threats.
Overcoming Legacy Hurdles in Bounty Design
Legacy programs drowned in AI noise and verification drudgery. ZK proofs fix that, as Forbes argues, with bonuses for proof-backed submissions elevating quality. Daniel Rodríguez's Medium vision of ZK courts for AI agents takes it further: prove your compute spend, claim the bounty. No more phantom efforts.
In practice, sybil resistant bounties demand hybrid setups. AI handles behavioral biometrics and challenge-response; ZK wraps it in privacy. Costs plummet - no central auditors, just decentralized trust. Platforms scale to millions without spam overload, fostering genuine collaboration.
Essential Anti-Spam Features
- AI Anomaly Detection: Leverages AI to identify bots via human-centric challenges like the Human Challenge Oracle (HCO), making fake identities costly ([arxiv]).

- ZK Uniqueness Proofs: Enables privacy-preserving verification of unique attributes without revealing data, as in zkVerify for fraud prevention ([zkVerify]).
- On-Chain Reward Disbursement: Automates fair payouts to verified contributors in bug bounty programs like HackenProof and Hashlock.

- Adaptive Challenge Engines: Deploys time-bound cognitive challenges solvable by humans but hard for bots, enhancing Sybil resistance.

- Compliance-Ready zkKYC: Provides private identity proofs meeting regulations, e.g., zkMe's zkKYC and Cysic-Billions partnership ([source]).

As adoption accelerates, expect zkverifiedtasks. com to set benchmarks. Collaborations like Cysic and Billions Network pave the way, hardware-accelerating ZK for real-time checks. HackMD's ZKML bridge unlocks AI models provably trained on private data, perfect for nuanced bounty scoring.
This ecosystem thrives because it aligns incentives. Hunters invest effort knowing payouts are secure; projects save on fraud losses. From equities to crypto, I've seen trust as the ultimate alpha generator. Here, AI and ZK proofs deliver it at scale, turning Web3 bounties into meritocracies where ingenuity always cashes out.





No comments yet. Be the first to share your thoughts!