Zero-Knowledge Proofs for Preventing Double Claims in Web3 Bug Bounties

In the high-stakes world of Web3 bug bounties, where ethical hackers hunt vulnerabilities for hefty rewards, double claims poison the well. Imagine two researchers independently spotting the same smart contract flaw; the first submits, but the second sneaks in ahead through timing tricks or insider leaks. Disputes erupt, trust erodes, and platforms bleed resources resolving who gets paid. Enter zero-knowledge proofs (ZKPs), the cryptographic wizards enabling zk proofs bug bounties and pioneering double claim prevention in Web3. These proofs let finders verify submission uniqueness and timeliness on-chain without exposing sensitive exploit details, slashing fraud while safeguarding privacy.

Traditional bug bounty programs, from Immunefi to HackerOne’s Web3 arms, grapple with opacity. Submitters often withhold full PoCs until payout, breeding suspicion. Platforms timestamp reports off-chain, but blockchain immutability demands better. As Forbes notes, ZKPs act like superheroes, proving knowledge of a secret – the vuln – sans revelation. This shifts secure bounty verification from human arbitration to math.
The Double Claim Dilemma Exposed
Double claims aren’t rare; they’re systemic. In crowded fields like DeFi audits, multiple teams probe the same codebases. A 2023 Medium piece on revolutionary platforms highlighted how transparency curbs duplicates, yet most systems falter. Researchers verify submissions manually, cross-checking hashes or descriptions, but edge cases abound: paraphrased reports, partial disclosures, or coordinated rings. Web3 amplifies this with pseudonymous actors and global time zones, where “first” blurs.
Costs mount fast. Platforms reject duplicates post-facto, alienating talent. Payouts split or withheld spark backlash on Twitter and Discord. Worse, delayed verification leaks vulns, inviting exploits before patches. Hacken. io underscores ZKPs’ role in proving execution privately, ideal for bounties where details stay secret until triage.
Enter zkPull from HackQuest, a trustless protocol auto-rewarding pulls via ZK. Developers prove contributions without custody battles. Yet, core platforms lag, relying on centralized judges. ZKPs flip this: prove “I found it first and uniquely” via succinct proofs, verifiable by anyone, revocable by none.
Unpacking Zero-Knowledge Proof Mechanics
At heart, a ZKP lets prover convince verifier of a statement’s truth without extra info leakage. Classic example: prove you know a Sudoku solution sans showing the grid. In formal terms, from Cyfrin’s deep dive, it’s three properties – completeness (honest prover succeeds), soundness (cheaters fail), zero-knowledge (verifier learns nothing beyond truth).
Modern flavors like zk-SNARKs (Succinct Non-interactive ARguments of Knowledge) power this. Prover generates a tiny proof from witness data (vuln details), verifier checks in milliseconds. TokenMinds flags cross-chain potential, reconciling formats via ZK. For bounties, hash the vuln descriptor, timestamp via blockchain oracle, then prove hash matches secret without revealing it.
Deploying ZKPs: Platforms Leading the Charge
Remedy blazes trails, timestamping submissions via advanced ZK on blockchain. Ethical hackers prove possession of unique vulns; duplicates fail verification instantly, disputes vanish. zkpoex ups the ante: submit crypto proofs sans exploit code, claim rewards on verification. Payouts instant, privacy ironclad – a bounty hunter’s dream.
Yet pitfalls lurk. Cantina. xyz warns of overlooked flaws; a snarkjs typo enabled fake proofs, per recent audits. Meticulous coding, formal verification, and continuous audits are non-negotiable. ZKML bridges AI/ML for smarter verification, analyzing proofs without data peeks, per HackMD. These evolutions cement ZKPs as double claim prevention Web3 bedrock, rewarding true innovators while sidelining copycats.
While these advancements propel zk proofs bug bounties forward, the path isn’t without thorns. Recent scrutiny revealed a snarkjs library flaw – a mere typographical error – that let attackers forge proofs, highlighting how even tiny oversights can undermine trust. Platforms like Remedy counter this by layering ZK timestamps atop blockchain oracles, ensuring submissions etch immutably without vuln exposure. zkpoex takes it further, letting hackers prove ethical claims cryptographically, payouts flowing on verification alone. Such innovations don’t just patch holes; they rebuild the incentive structure from tamper-proof foundations.
Navigating ZKP Challenges Head-On
Critics balk at ZKPs’ complexity, citing steep learning curves and gas costs. zk-SNARKs demand custom circuits, devouring weeks for bespoke vuln proofs. Verifiers balloon smart contract sizes, hiking deployment fees on Ethereum. Yet, layer-2 scaling and recursive proofs slash this; Polygon or Optimism host verifiers dirt-cheap. Cantina’s auditors flag common blind spots like improper field arithmetic or trusted setup leaks, but tools like Circom and formal provers mitigate risks. I argue these hurdles pale against the alternative: endless arbitration draining treasuries and morale.
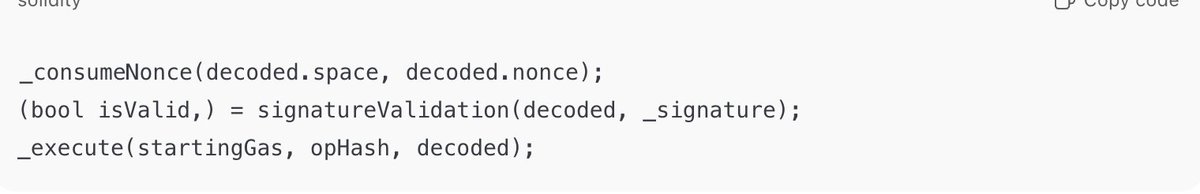
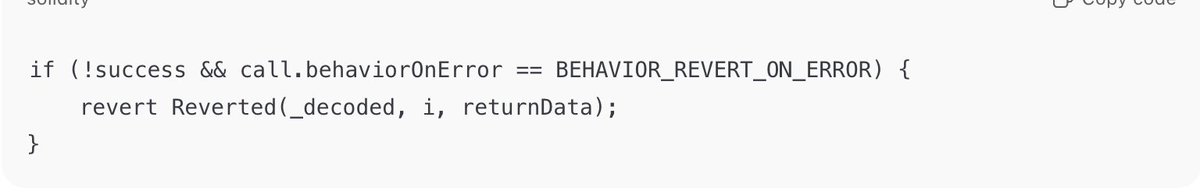
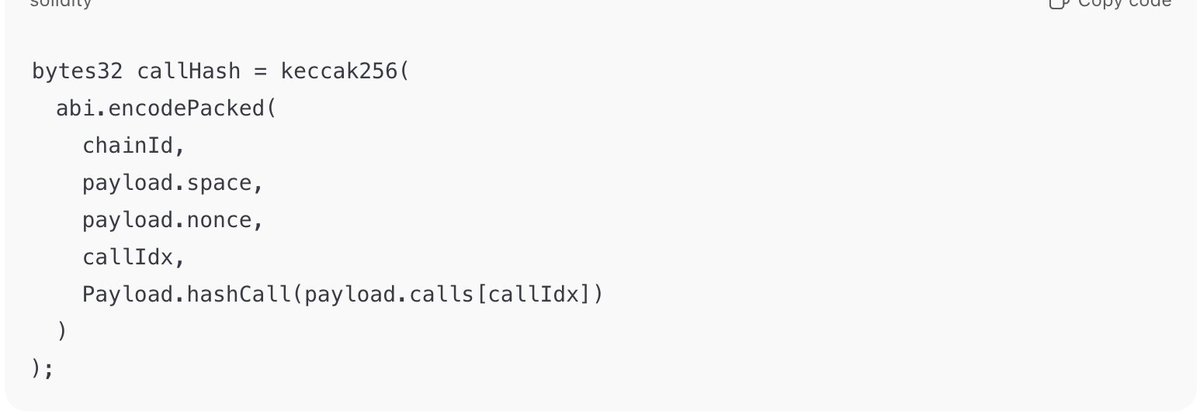
Consider the workflow. A hunter crafts a commitment hash of their PoC, submits it with a ZK proof tying it to the current block. The contract verifies uniqueness against a Merkle tree of priors, rewarding only novel hashes. No central party peeks; math enforces fairness. Hacken’s breakdown shows ZKPs proving execution privately, perfect for vulns where early disclosure risks copycats. This isn’t theory – zkPull automates rewards for contributions, extending bounties to open-source pulls sans disputes.
The Road Ahead: ZKPs as Bounty Standard
Picture 2026: every major Web3 bounty runs ZKP-native. Immunefi integrates succinct proofs; Code4rena timestamps audits cryptographically. Double claims? Relics of Web2. Hunters focus on discovery, not racing insiders. Platforms scale bounties to millions, fraud-proof via math. Humanity Protocol’s zkProofers evolve to sybil-resistant eligibility, ensuring one-human-one-claim. Challenges persist – quantum threats loom, but post-quantum ZK variants advance rapidly.
This shift demands collaboration: devs honing circuits, auditors probing edges, protocols subsidizing tooling. zkverifiedtasks. com exemplifies this synergy, blending AI triage with ZK for privacy-first verification. Ethical hackers thrive, projects harden faster, Web3 matures. In a pseudonymous arena rife with grift, ZKPs enforce meritocracy. Platforms embracing secure bounty verification today command tomorrow’s loyalty; laggards face exodus. The proof, quite literally, is in the protocol.