In the high-stakes world of Web3 bounties, where developers and ethical hackers chase rewards for uncovering vulnerabilities or completing complex tasks, trust is both the currency and the Achilles' heel. Traditional verification processes expose sensitive code, invite fraud, and drag on for days; a Forbes report highlights how even top bug bounty programs take one to ten days just to confirm a single report. Enter zero-knowledge proofs (ZKPs), a cryptographic marvel that promises zk proofs bounty verification without sacrificing the prover's secrets. As a risk specialist who's built models to shield against unseen threats, I see this as a game-changer for web3 bounty fraud prevention.

Consider the vulnerabilities in current setups. Bounty hunters submit code snippets or detailed exploits, laying bare intellectual property that competitors or bad actors could pilfer. Payouts stall amid manual reviews, breeding disputes and deterring talent. Platforms like Immunefi's zkVerify bounties nod to offloading proof verification, yet the industry grapples with scalability and privacy. Reddit threads question why programs wouldn't embrace ZKPs to prove a bug exists sans disclosure; it's a valid puzzle, one that underscores systemic blind spots.
Verification Delays Plaguing Traditional Bug Bounties
Delays aren't mere inconveniences; they erode program efficacy. CertiK's advances in formal verification for ZK circuits signal readiness, but legacy systems lag. A vulnerability report demands triage, reproduction, and impact assessment, often spanning weeks. Payouts? Infamously erratic. Remedy, touted in Medium and YouTube as a revolutionary Web3 bounty platform, dangles big rewards with less competition, yet relies on advanced ZK tech for transparency. Without it, fraud festers: fake submissions, duplicated claims, or withheld fixes until payout.
This friction stifles innovation. Developers hesitate to engage, fearing IP theft, while projects bleed resources on audits. My stress-testing experience reveals parallels to market crashes: unchecked risks compound quietly until they don't. Privacy preserving task proofs via ZKPs flip the script, allowing provers to demonstrate task completion cryptographically, verifier nods yes or no, secrets stay sealed.
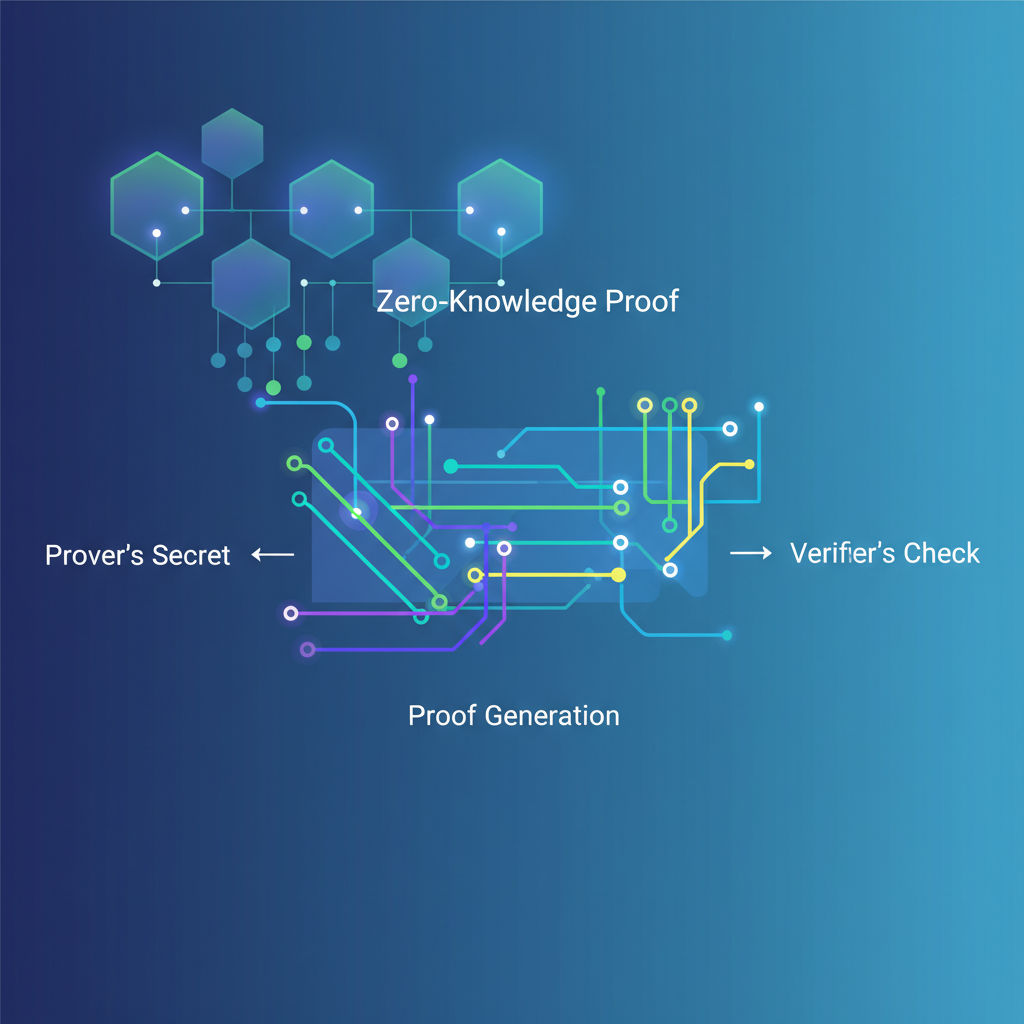
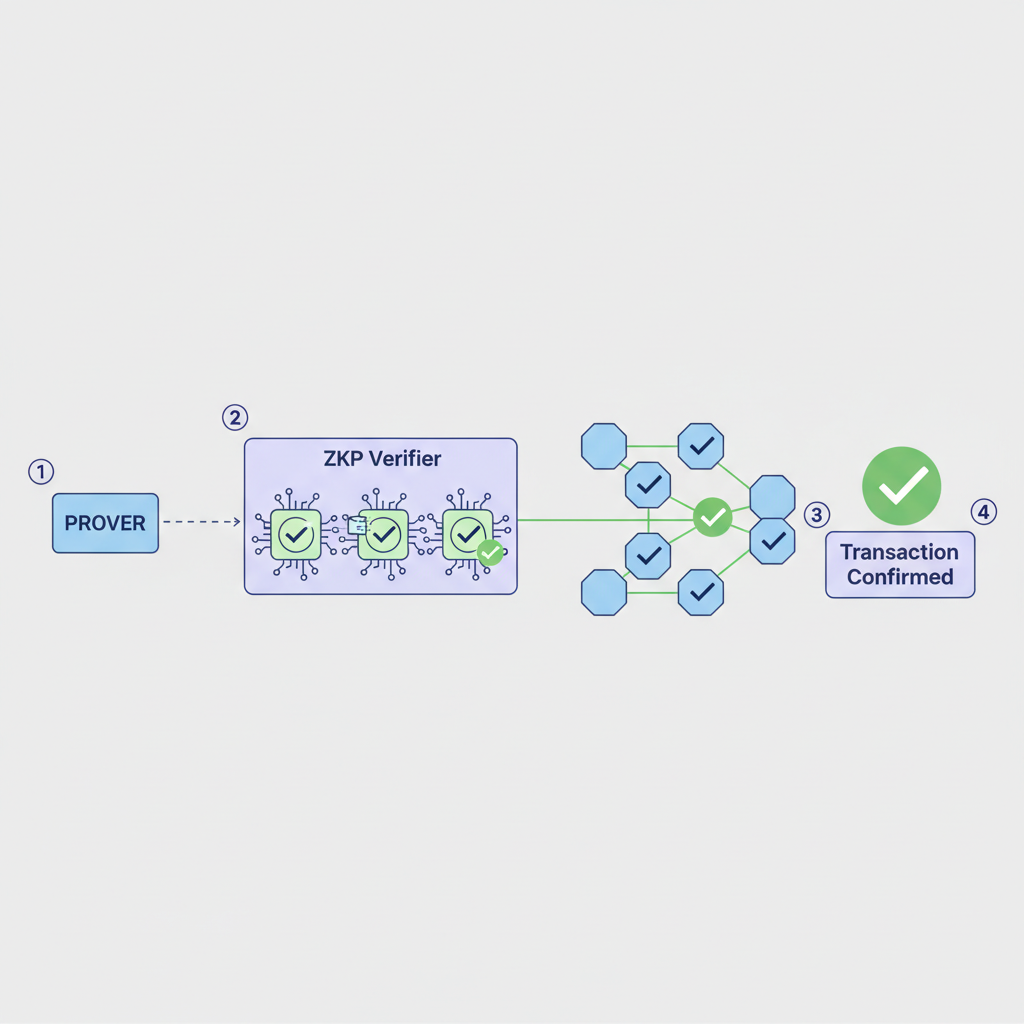
Demystifying Zero-Knowledge Proofs for Task Verification
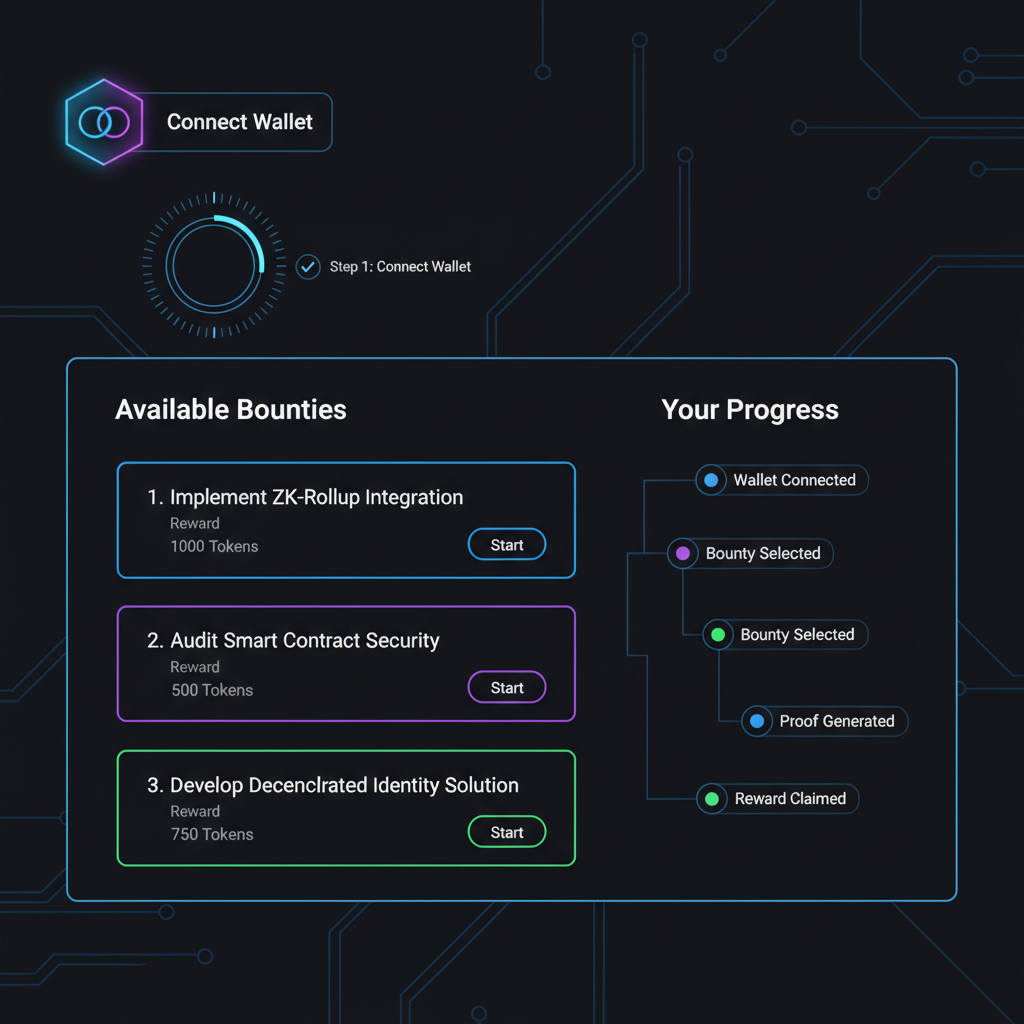
ZKPs, as Midnight Docs and Dock Labs explain, let you prove knowledge without spilling it. Prover convinces verifier of a statement's truth minus underlying data. In bounties, imagine proving 'I fixed the smart contract overflow' via a proof, no code shared. Togggle's take on Web3 identity security aligns: one party proves value knowledge to another, sans revelation.
Key ZK Task Completion Advantages
- Fraud-proof verification: Cryptographically confirms task completion without trusting submitters, addressing delays in bug bounties (1-10+ days per Forbes).
- IP protection: Provers submit ZKPs without revealing code or vulnerabilities, safeguarding sensitive data as in zkVerify and Remedy platforms.

- Instant scalability: Offloads heavy proof verification to chains like zkVerify's Substrate blockchain, enabling modular networks to scale efficiently.
- Cost efficiency for platforms: Reduces expensive on-chain verification costs, as demonstrated by zkVerify and ZKBounty for Web3 bounties.
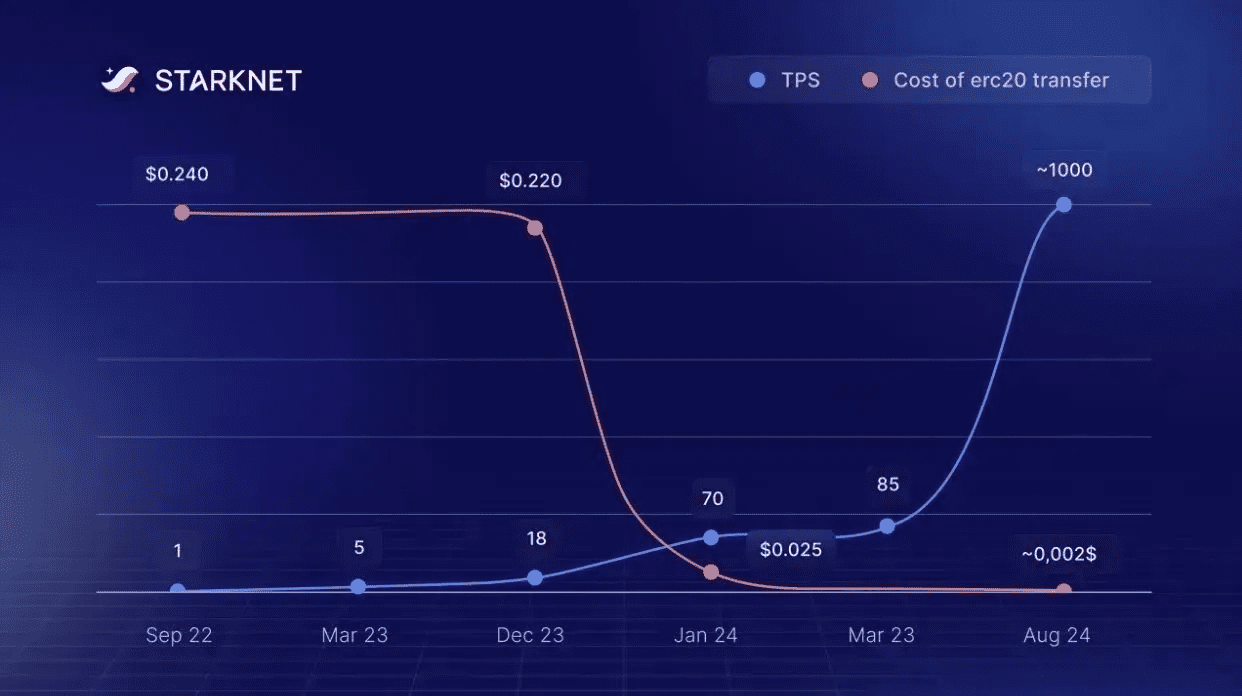
Updated contexts spotlight traction. zkVerify's Substrate blockchain slashes verification costs for modular networks. ZKBounty and zKontract let devs claim via proofs, privacy intact. BlockBounty and zkpoex empower hackers to submit ZKP-backed bugs ethically. These aren't hypotheticals; they're live, bridging AI/ML with Web3 per HackMD's ZKML vision.
Platforms Pioneering ZK-Enabled Bounty Ecosystems
Remedy leads with substantial rewards and ZK transparency, minimizing disputes. zkVerify's Immunefi integration offloads heavy computation, expanding Web3's cryptographic toolkit. GitHub repos and EthGlobal showcases for ZKBounty reveal modular designs for seamless integration. Devpost's BlockBounty uses ZKPs for secure vuln submissions, verifying existence without exposure.
Yet caution tempers optimism. Formal verification remains nascent; CertiK's breakthroughs help, but circuit complexity risks flaws. Scalability demands efficient provers, lest gas fees devour rewards. In my hedging playbook, we protect downside first: ZKPs demand rigorous audits before prime-time bounty reliance. Still, for zero knowledge task completion, they forge trustless rails where none existed, potentially halving verification times and slashing fraud by orders of magnitude.
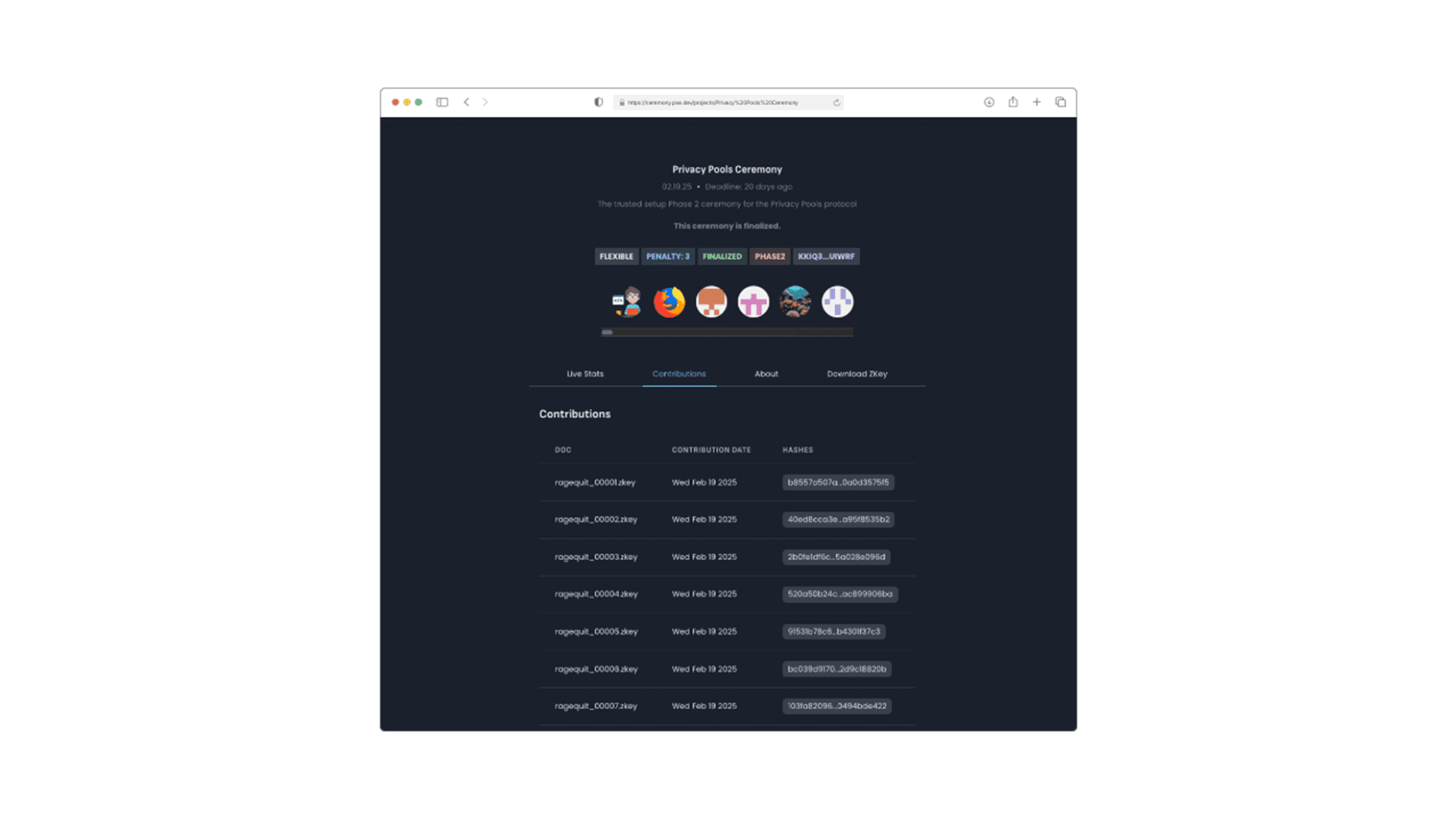
Implementing ZKPs starts with circuit design tailored to the bounty task. For a smart contract audit, the circuit encodes checks like 'vulnerability X is present and exploitable with input Y, ' generating a proof verifiable on-chain. Tools from zkVerify streamline this, offloading computation to their chain while keeping proofs succinct. In practice, a hunter generates the proof locally, submits a hash or public inputs to the bounty smart contract, which verifies in seconds via a trusted setup or universal prover. No code, no exploits shared until post-payout if opted.
This workflow resonates with my risk models: isolate variables, test extremes, verify outputs. Platforms like ZKBounty showcase it via EthGlobal hacks, where proofs claim rewards autonomously. BlockBounty's Devpost entry proves ethical hacking's pivot; submit a ZKP affirming 'bug triggers loss Z under condition W, ' platform pays out blindly. Fraud? Near impossible, as invalid proofs fail mathematically. Yet, my FRM lens spots shadows: soundness relies on circuit correctness. A flawed circuit equals a backdoor.
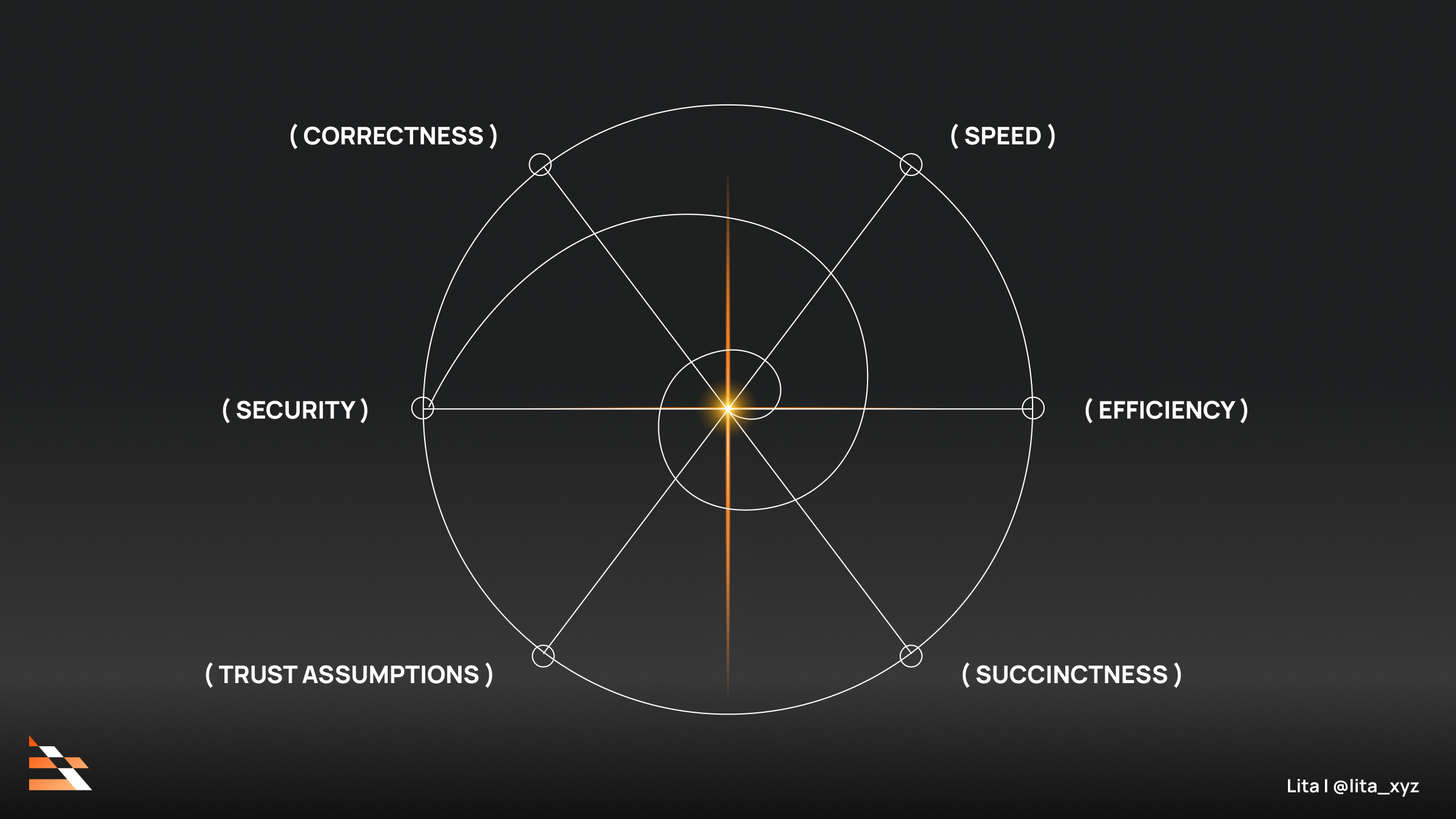
Navigating Risks in Privacy Preserving Task Proofs
Caution defines adoption. Proving time explodes for complex tasks, demanding SNARKs or STARKs optimizations. Gas costs, though dropping with zkVerify, still pinch small bounties. Quantum threats loom distant but real; post-quantum ZK variants emerge slowly. Reddit's cryptography skeptics probe deeper: why not full disclosure post-proof? Fair point, but in competitive Web3, leaks kill velocity. My mantra applies: protect downside. Mandate multi-auditor circuit reviews, hybrid proofs with minimal disclosure, and insurance pools for false positives.
Essential ZK Bounty Safeguards
- Circuit Formal Verification: Rigorously prove ZK circuit soundness to avert hidden flaws. CertiK advances standards for complex circuits, reducing verification risks.

- Multi-party Computation Setups: Secure trusted setups via distributed ceremonies, minimizing trust assumptions. Powers of Tau MPC for Groth16 exemplifies caution against single-party compromise.
- On-chain Proof Registries: Immutable blockchain storage for verifiable proofs. zkVerify's Substrate chain enables efficient, low-cost verification in Web3.

These mitigations echo hedging strategies I've crafted across volatile markets. Diversify proof types, stress-test circuits like portfolios under crash scenarios. CertiK's formal verification milestones pave the way, proving complex circuits airtight. Immunefi's zkVerify bounties test waters, offloading verification to cut expenses by 90% in modular chains. Remedy's allure grows: hefty payouts, low noise, ZK backbone ensuring web3 bounty fraud prevention.
The Road Ahead for Zero Knowledge Task Completion
Vision sharpens with ZKML's fusion, per HackMD. AI analyzes code privately, spits ZKPs for bounty claims, revolutionizing ML-Web3 bridges. Imagine bounties for model fine-tuning: prove accuracy gains without dataset exposure. Platforms evolve; zkpoex hints at DEX bounties verified cryptographically. Scalability surges via recursive proofs, compressing verifications into Ethereum blocks effortlessly.
From my vantage, after 16 years modeling black swans, ZKPs aren't hype; they're infrastructure. They dismantle verification bottlenecks, empowering a meritocracy where skill, not exposure, claims rewards. Developers flock unburdened, projects scale audits exponentially. Friction fades, trust blooms cryptographically. In Web3's wilds, where code is king and secrets gold, privacy preserving task proofs erect the walls needed for sustainable growth. The upside? Bounties multiply, innovation accelerates, and fraud's graveyard grows. Just ensure those walls are forged in verified steel.










No comments yet. Be the first to share your thoughts!