ZKML for Privacy-Preserving AI Task Verification in Web3 Bounties

In the cutthroat landscape of Web3 bounties, developers and ethical hackers pursue multimillion-dollar rewards for uncovering vulnerabilities or completing complex tasks. Yet, fraud undermines this ecosystem: fake submissions, Sybil attacks, and unverifiable AI-assisted work erode trust and inflate costs. Zero-Knowledge Machine Learning, or zkML, emerges as the strategic antidote, enabling privacy-preserving AI task verification that proves legitimacy without exposing sensitive data or computation details.

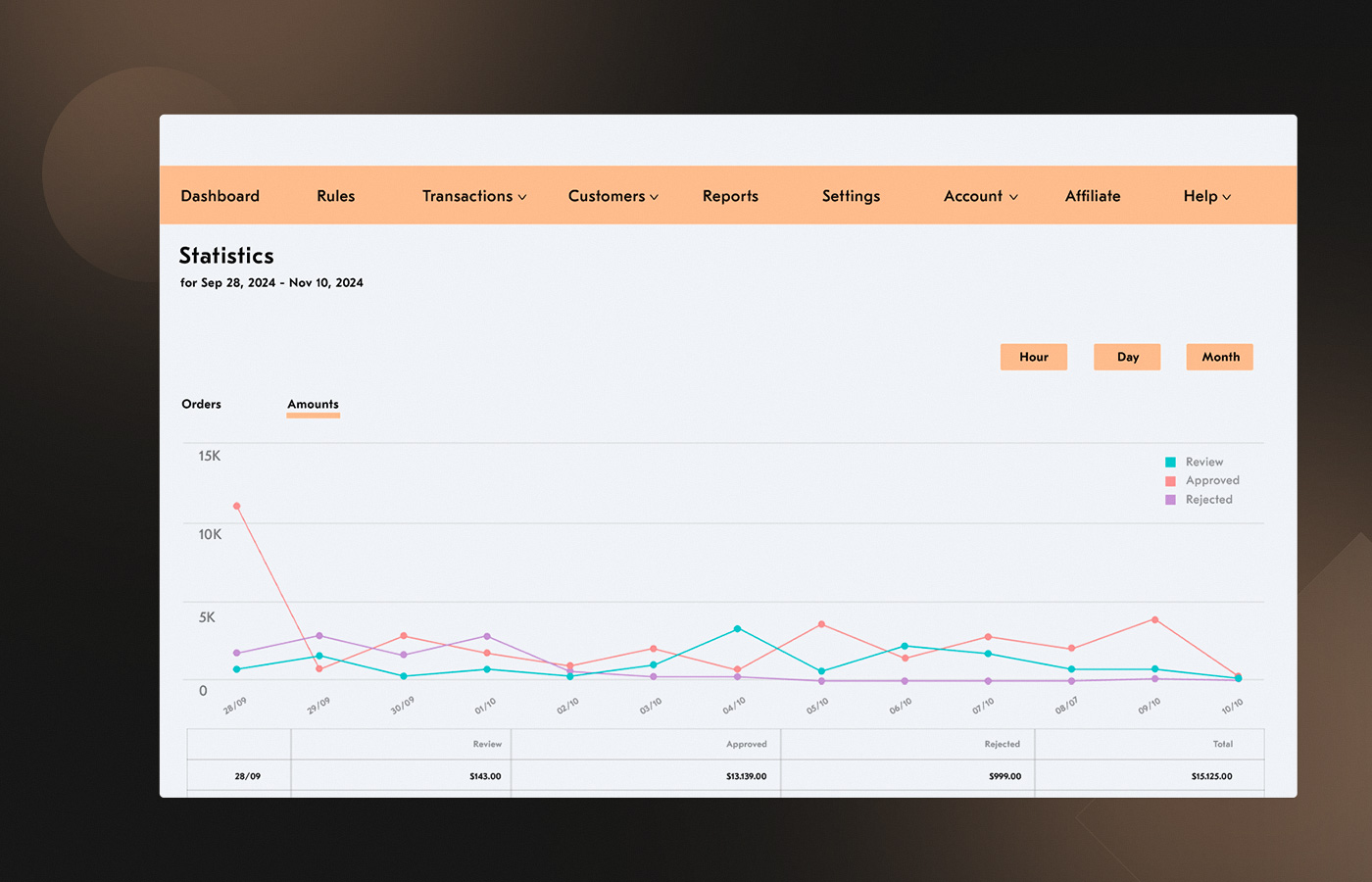
Platforms like zkverifiedtasks. com already leverage AI and ZK proofs for fraud-proof verification, but scaling to high-volume bounties demands more. Traditional methods falter under spam and privacy leaks; zkML fuses cryptographic rigor with machine learning inference, creating verifiable proofs of correct AI outputs. This isn’t hype; it’s a data-backed shift, as seen in anomaly detection models trained on blockchain data to flag exploits instantly.
Fraud Vulnerabilities Exposing Web3 Bounties to Risk
Web3 bounties mirror high-frequency trading in their speed and stakes, yet lack robust safeguards. Sources highlight recurring issues: Block Trix-style fraud in reward payouts, Sybil attacks inflating participant counts, and unproven AI contributions masquerading as human effort. Anomaly detection via linear models and decision trees, as discussed at ETHSANFRANCISCO, targets these, but without zero-knowledge, they expose user strategies or proprietary models.
Core Fraud Risks & zkML Fixes
-
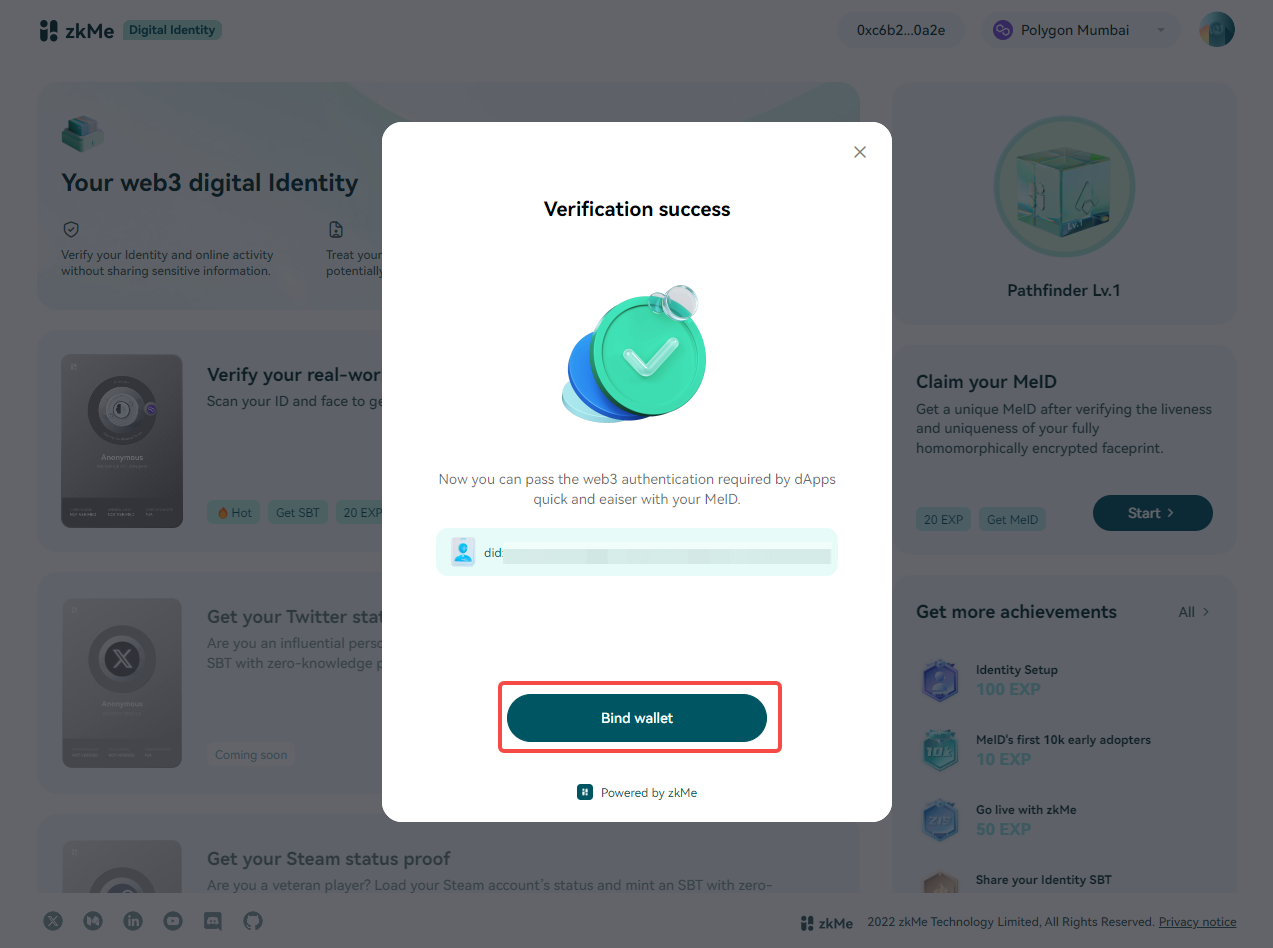
Sybil Attacks: Prevented with identity ZK proofs like zkMe’s zkKYC for decentralized verification without revealing data.
-
Fake Submissions: Verified via AI inference ZK proofs using Jolt Atlas framework for privacy-preserving model outputs.
-
Exploit Plagiarism: Detected with anomaly ZK proofs from zkML fraud models, as in awesome-zkml for exploitability checks.
-
Reward Spam: Curbed by scalable on-chain verification with zkVerify reducing costs 90%+ for high-volume bounties.
Strategically, these vulnerabilities compound. A single undetected fraud can cascade, deterring legitimate hunters and bloating smart contract gas fees. Real-time crypto fraud models analyze transactions for patterns, but zkML elevates this by sealing computations in cryptographic envelopes, preventing network-level deception while safeguarding privacy.
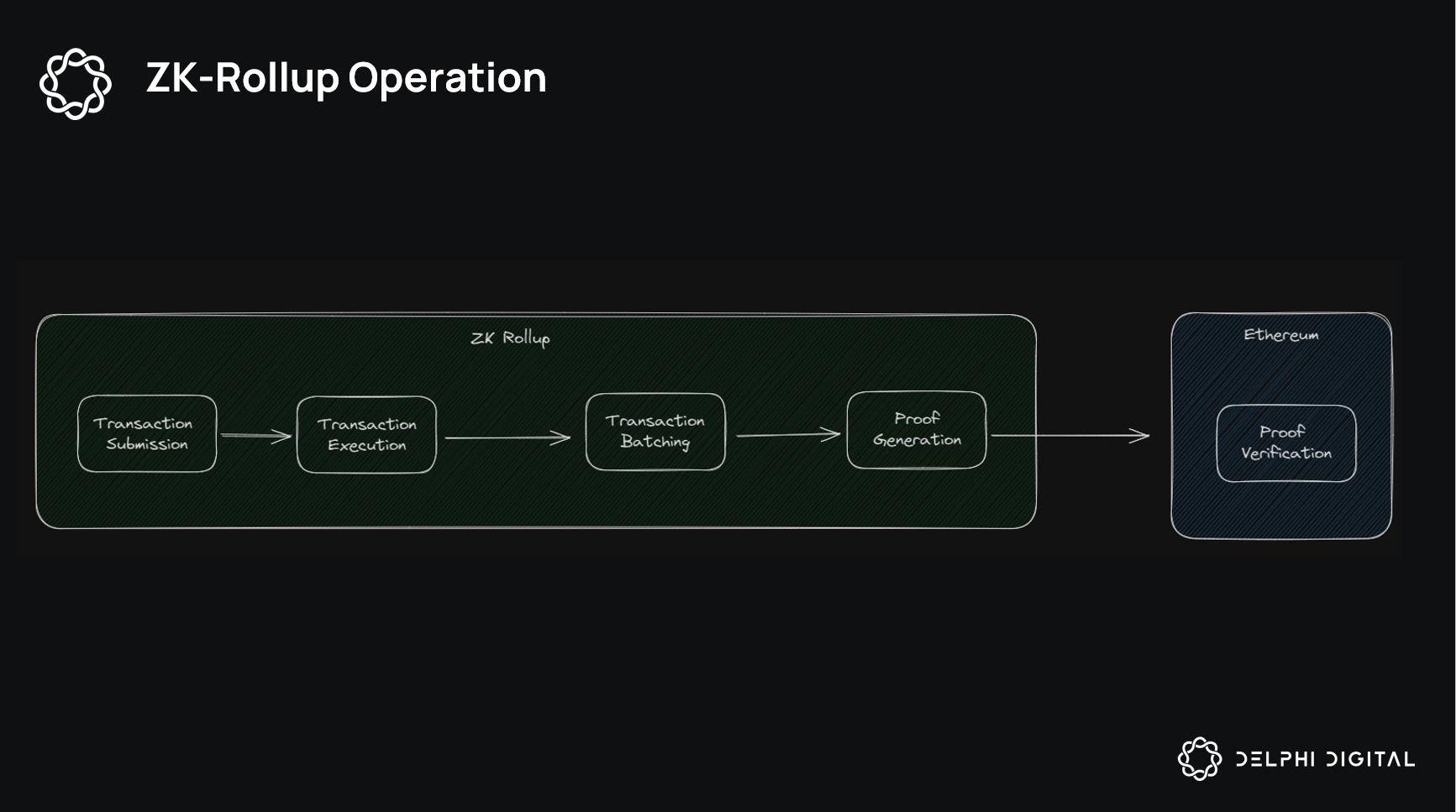
ZKML Mechanics for Trustless AI Verification
At its core, zkML task verification proves that an AI model processed inputs correctly and output expected results, all without revealing the model weights, inputs, or intermediate steps. Provers generate succinct non-interactive arguments of knowledge (SNARKs) for ML inference, verifiable on-chain at minimal cost. This aligns perfectly with AI zk proofs bounties, where bounty platforms demand proof-of-work without privacy trade-offs.
Consider fraud detection: train models on smart contract data to suspend suspicious actors, then zk-prove the inference. Worldcoin’s awesome-zkml repo outlines ZK anomaly detection for exploits, enabling proofs of fraud without data leaks. Binance notes zkML’s role in Sybil prevention, training on-chain data for proactive security. Opinionated take: this isn’t incremental; it’s transformative, turning bounties from trust-mined lotteries into efficient, scalable markets.
2026 Catalysts Accelerating zkML Adoption
Recent breakthroughs position zero knowledge machine learning web3 for dominance. Artemis’s Commit-and-Prove SNARKs slash prover costs for large models, tackling commitment verification in pipelines. Jolt Atlas extends proving to inference, yielding verifiable AI sans data exposure. zkMe’s zkKYC fuses ZK with compliance for identity verification, vital for bounty eligibility.
Polyhedra’s EXPchain Testnet V3 launches ‘Explicity, ‘ hardware-accelerated for real apps. zkVerify cuts costs 90% with Groth16 support, boosting interoperability. These aren’t lab curiosities; they’re production-ready, as Cortex Labs demonstrated with multi-modal models for recommenders and fraud. In bounties, this means privacy preserving AI verification at scale, supporting high-volume rewards without fraud dilution.
Macro view: interconnected markets demand such tools. As Web3 bounties grow to rival TradFi bug programs, zkML ensures fraud proof bounties zk become standard, preserving capital flows and developer incentives.
Platforms that integrate zkML task verification today gain a defensible moat, outpacing rivals mired in manual audits or oracle-dependent checks. zkverifiedtasks. com exemplifies this edge, blending AI anomaly detection with ZK proofs to validate submissions in real time, much like real-time crypto fraud models scanning blockchain patterns for instant flags.
Integrating zkML: A Practical Blueprint for Web3 Bounties
Bounty operators face a strategic choice: cling to vulnerable systems or deploy zkML for web3 bounty verification zkML. The mechanics scale seamlessly. Developers submit AI-assisted tasks; the platform runs inference inside a zkML circuit, generating a proof attesting to correct execution. Verifiers check the SNARK on-chain, disbursing rewards only for valid proofs. No more disputes over “plagiarized” exploits or ghost submissions.
This workflow, powered by tools like Polyhedra’s Explicity testnet, handles thousands of submissions daily without gas bloat. Strategically, it mirrors risk parity in portfolios: diversify verification across ZK layers to hedge fraud exposure. Early adopters, drawing from zkMe’s zkKYC for eligibility checks, report 90% cost drops via zkVerify’s Groth16 optimizations.
Quantifying the Edge: Data-Driven zkML Impact
Empirical signals abound. GitHub’s awesome-zkml repo details ZK fraud proofs for exploits, trainable on historical bounty data to preempt Sybil swarms. ResearchGate’s blockchain-AI fusion cuts insurance fraud analogs by integrating verifiable claims; apply this to bounties, and dilution plummets. Cortex Labs’ linear models already nail fraud detection, but zkML adds privacy seals, echoing Worldcoin’s on-device proofs that thwart network cheats.
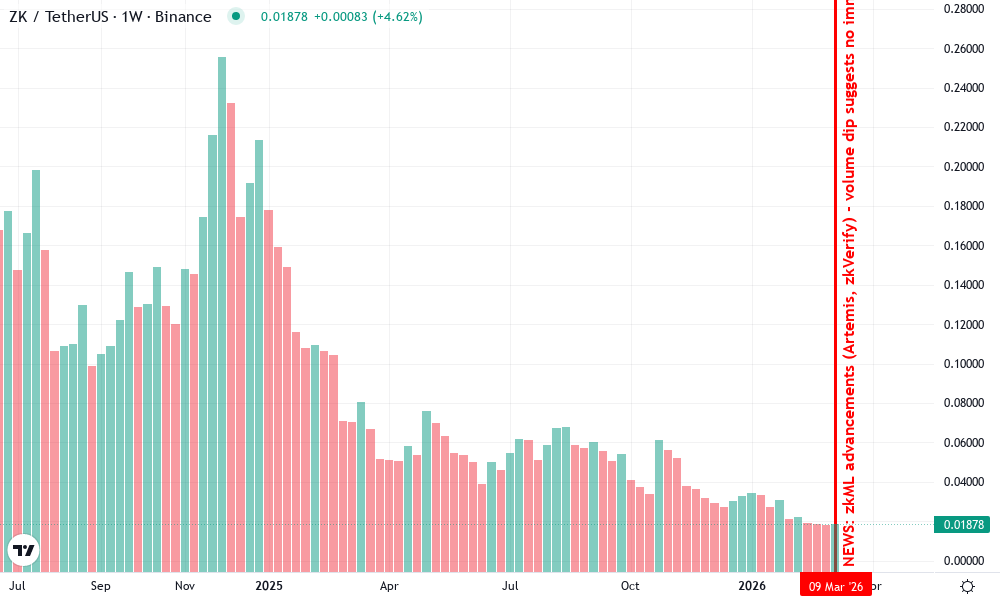
zkSync Token (ZK) Technical Analysis Chart
Analysis by William Brown | Symbol: BINANCE:ZKUSDT | Interval: 1W | Drawings: 5
Technical Analysis Summary
In my conservative style as a macro strategist, draw a prominent downtrend line connecting the early 2026 volume peak at approximately 2.80 (2026-01-10) to the recent lows around 0.50 (2026-04-15), using ‘trend_line’ to highlight waning momentum. Add horizontal_lines at key support 0.40 and resistance 0.70 for clear S/R visualization. Use rectangles to box the distribution range from mid-February to mid-March 2026 between 1.50-0.80. Place callouts on declining volume bars noting ‘distribution phase post-zkML hype’ and a downward arrow marker on MACD bearish signal. Text annotations for low-risk entry zone at 0.42 with stop below 0.38. Vertical line at 2026-03-14 for zkML news event.
Risk Assessment: medium
Analysis: Declining volume contradicts strong zkML fundamentals, raising cycle top risk in interconnected Web3 markets; low tolerance warrants confirmation
William Brown’s Recommendation: Remain sidelined in cash equivalents until volume uptick confirms reversal – prioritize risk parity
Key Support & Resistance Levels
📈 Support Levels:
-
$0.4 – Recent volume trough aligning with potential price floor amid zkML support
moderate -
$0.35 – Psychological low if breakdown occurs
weak
📉 Resistance Levels:
-
$0.7 – Prior swing low now resistance on declining volume
moderate -
$1 – Mid-range barrier from Feb consolidation
weak
Trading Zones (low risk tolerance)
🎯 Entry Zones:
-
$0.42 – Bounce from support with positive zkML catalysts, low-risk dip buy
low risk
🚪 Exit Zones:
-
$0.65 – Measured move target from range height
💰 profit target -
$0.38 – Tight stop below support to preserve capital
🛡️ stop loss
Technical Indicators Analysis
📊 Volume Analysis:
Pattern: declining after initial spike
High volume early 2026 (Jan-Feb) followed by lower highs/lows, classic distribution signaling lack of sustained interest
📈 MACD Analysis:
Signal: bearish divergence
MACD histogram contracting with price/volume downtrend, no bullish crossover yet
Applied TradingView Drawing Utilities
This chart analysis utilizes the following professional drawing tools:
Disclaimer: This technical analysis by William Brown is for educational purposes only and should not be considered as financial advice.
Trading involves risk, and you should always do your own research before making investment decisions.
Past performance does not guarantee future results. The analysis reflects the author’s personal methodology and risk tolerance (low).
Opinion: skeptics decry prover latency, yet Artemis slashes it for large models, making zkML viable even for multi-modal recommenders in bounty matching. Platforms like Block Trix, plagued by payout scams, could pivot to this for fraud-proof scaling. The math checks out: verifiable inference preserves IP, as PolyhedraZK asserts, sealing evaluations against academic-style deceptions.
Strategic zkML Use Cases
-

Verifiable AI code reviews proving exploit novelty via ZK proofs of exploitability/fraud from worldcoin/awesome-zkml.
-
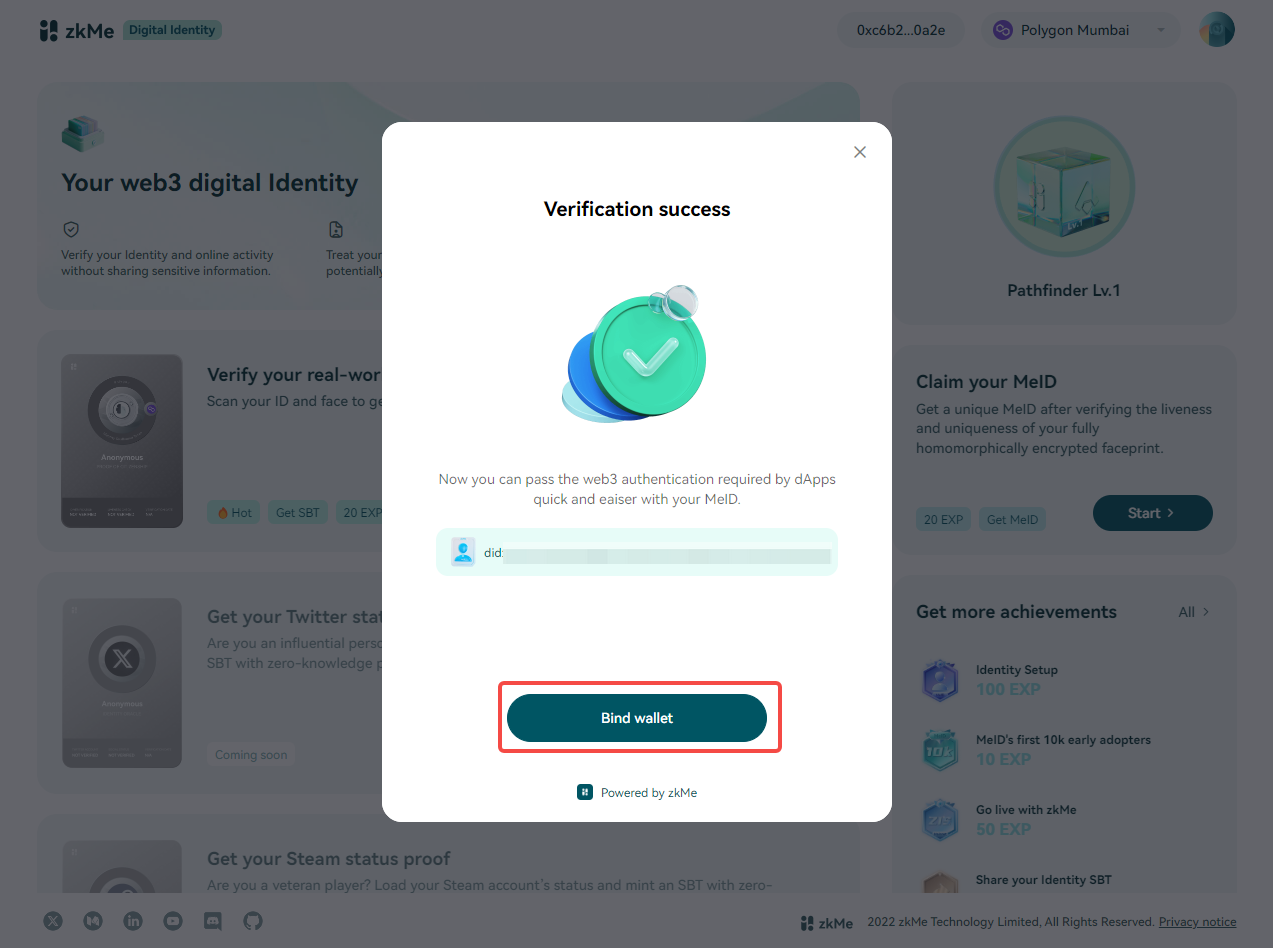
Privacy-preserving KYC for hunter eligibility using zkMe’s zkKYC Service with FATF-compliant ZK proofs. Source
-

Anomaly proofs detecting submission farms with AI models for fraud/Sybil prevention from zkverifiedtasks.com and PolyhedraZK.
-
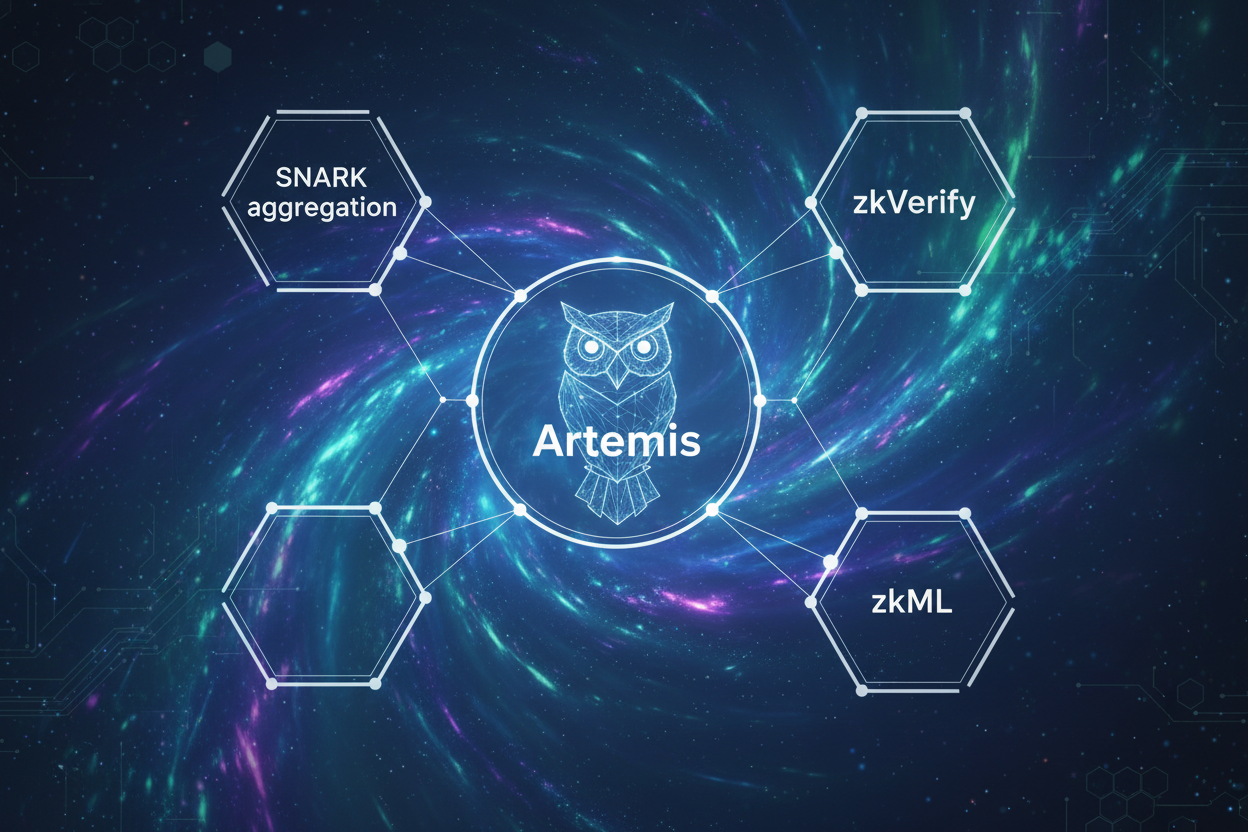
Scalable rewards via low-cost SNARK aggregation; zkVerify cuts costs 90%, Artemis Commit-and-Prove SNARKs enhance efficiency.
-
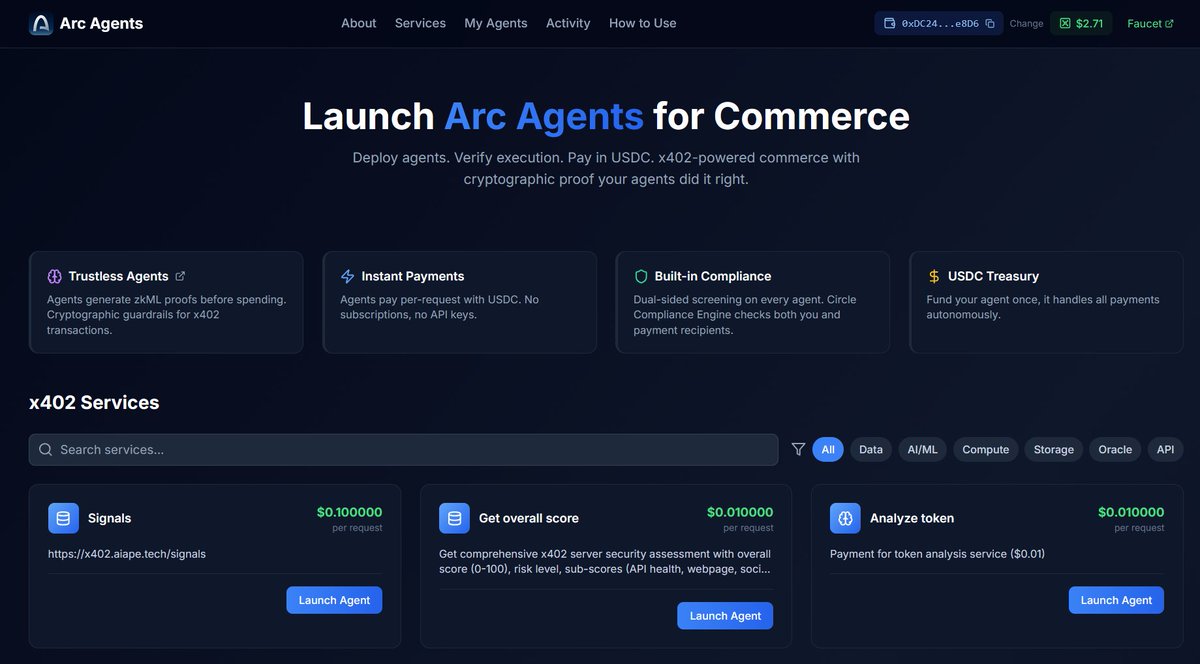
Autonomous agents with ZK-attested decisions using Jolt Atlas for verifiable AI inference and Polyhedra EXPchain testnet.
Hunters benefit too. Prove your AI edge without revealing strategies, turning bounties into pure skill arenas. Platforms capture value through network effects: more trust draws bigger pots, fueling virtuous cycles akin to DeFi yield farms but grounded in crypto primitives.
Forward-looking, zkML redefines AI zk proofs bounties as the backbone of decentralized intelligence. As Web3 bounties eclipse TradFi equivalents in volume, only zkML delivers the cryptographic certainty to sustain them. Developers flock to testnets like EXPchain, honing hardware proofs for tomorrow’s high-stakes hunts. This isn’t evolution; it’s the pivot that cements Web3’s legitimacy, one verified task at a time.