Scaling Bounty Programs in DeFi Projects with Privacy-Focused ZK AI Tech

DeFi projects thrive on innovation, but their bounty programs often buckle under the weight of rapid growth. As protocols scale to handle billions in total value locked, vulnerabilities multiply, and traditional bug bounty systems strain to keep pace. Enter privacy-focused ZK AI tech: a potent combination that promises to supercharge DeFi bounties scaling with ZK, slashing fraud while safeguarding researcher anonymity. Platforms like zkverifiedtasks. com lead this charge, blending zero-knowledge proofs with AI-driven analysis for tamper-proof task verification.
[youtube_video: Explanation of zero-knowledge proofs in securing bug bounties and enhancing DeFi scalability]
Cracks in the Foundation of Legacy Bounty Systems
Picture this: a whitehat hacker uncovers a critical exploit in a high-stakes lending protocol. Submitting it means exposing trade secrets, risking competitive sabotage or worse, blackhat exploitation before patches deploy. That’s the stark reality for many in DeFi today. Immunefi’s CEO, Mitchell Amador, highlights how AI tools have democratized hacking, dropping exploit costs to pennies and flooding bounty platforms with noise. Verification delays stretch weeks, eroding trust and deterring top talent.
Fraud runs rampant too. Sybil attacks, duplicate reports, and AI-generated spam overwhelm human reviewers, as noted in recent Forbes analysis. Researcher distrust festers when payouts falter amid opaque processes. LayerZero’s recent mandate for identity revelation underscores the tension: privacy clashes with accountability. In my 18 years managing portfolios through market tempests, I’ve seen parallels in risk assessment; unverified inputs breed portfolio blowups. DeFi bounties need a cryptographic overhaul to scale securely.
ZK Proofs: The Privacy Shield Bounty Hunters Crave
Zero-knowledge proofs flip the script on privacy ZK AI DeFi dynamics. These cryptographic marvels let hackers prove a vulnerability exists – without spilling exploit details. zkpoex exemplifies this: submit a proof, trigger automatic payouts upon verification, all while code stays concealed. BlockBounty takes it further, enabling secure submissions that balance transparency for projects with ironclad anonymity for finders.
StarkWare and Hacken. io emphasize ZK’s dual punch: scalability via succinct proofs of massive computations, plus confidential dealings. No more full disclosures inviting copycats. For DeFi protocols juggling millions in TVL, this means faster patching cycles and fortified trust. Opinion ahead: mandating identities, as LayerZero does, feels like a step backward in a pseudonymous ecosystem. ZK offers verifiable claims minus the exposure – the smarter path for bounty programs DeFi verification.
Aztec Labs’ $450,000 bounty underscores demand, but without ZK, such pots invite chaos. zkverifiedtasks. com integrates these proofs natively, ensuring only legit completions claim rewards via privacy-preserving checks.
AI’s Role in Taming the Verification Beast
ZK alone isn’t enough; AI sharpens the blade. Cantina’s platform deploys machine learning for instant report triage: flagging spam, deduplicating finds, prioritizing high-impact bugs. This isn’t hype – it’s battle-tested filtering that frees teams from drudgery.
Combine AI with ZK, and you get zkSecurity’s vision: agents hunting ZK circuit flaws autonomously, verified sans leaks. Blockchain App Factory spotlights AI agents wielding ZKPs for trusted autonomy across sectors. In DeFi, this duo scales bounties exponentially. Projects onboard thousands of hunters globally, confident in fraud-proof outcomes. I’ve long preached diversified risk in portfolios; here, diversified verification via AI-ZK hybrids preserves capital against unseen threats.
ZK AI Benefits for DeFi Bounties
-
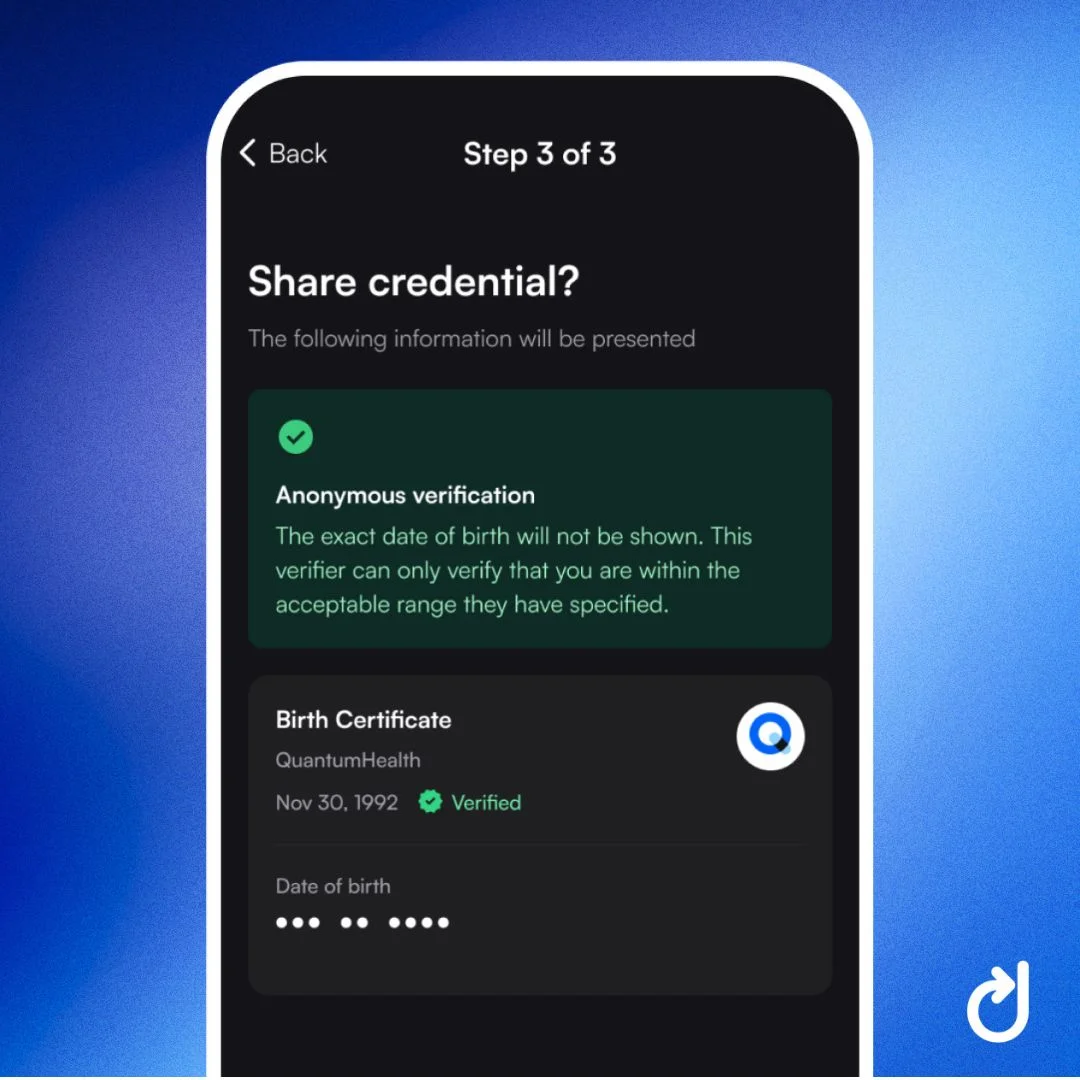
Privacy Protection: ZK proofs enable vulnerability submissions without revealing sensitive data, as in BlockBounty.
-

Spam Reduction: AI assesses report quality and deduplicates, filtering noise like Cantina‘s platform.
-
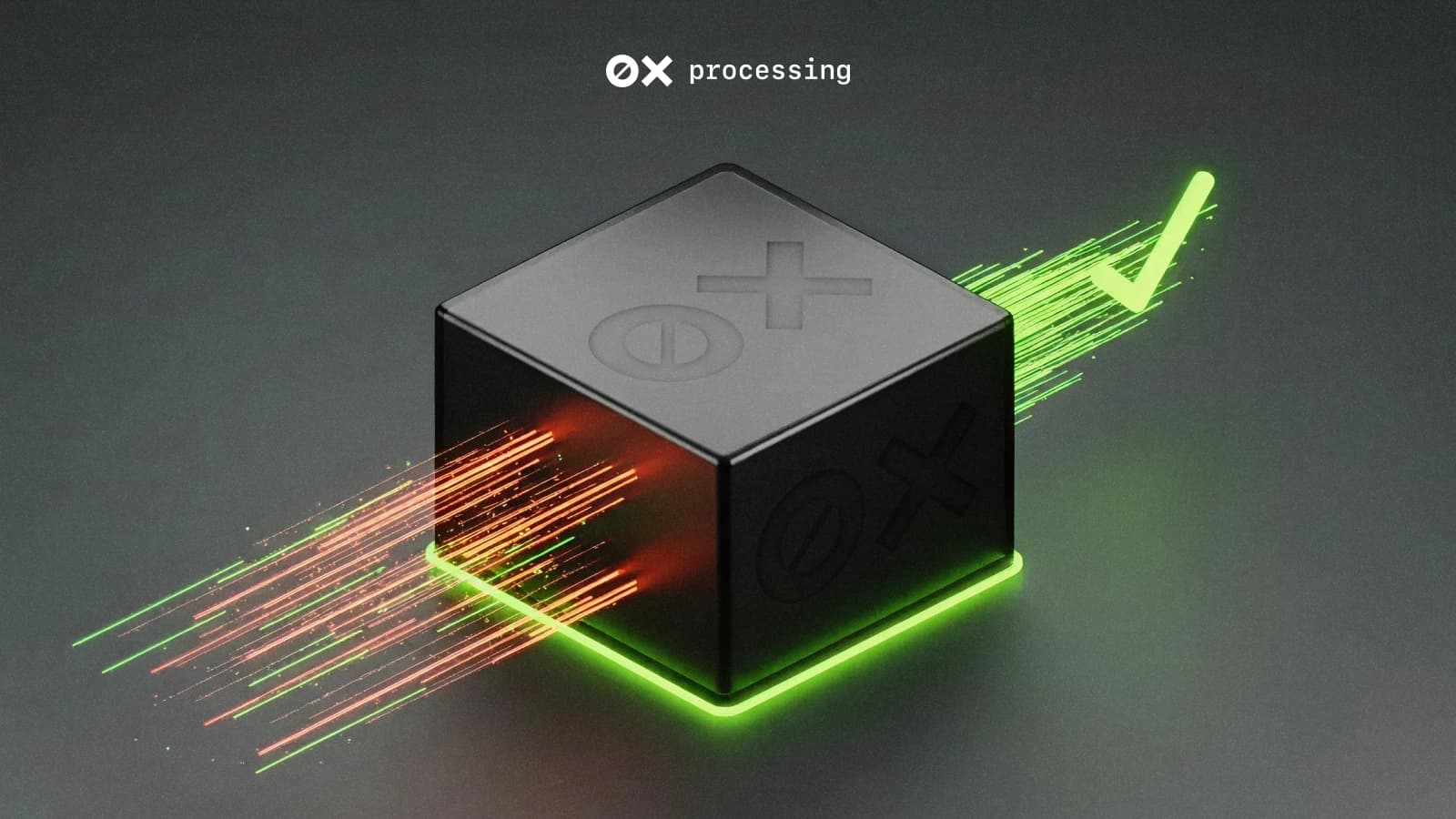
Auto-Payouts: Verified ZK proofs trigger automatic bounty payments via protocols like zkpoex.
-
Faster Verification: ZK enables swift validation of bugs without full disclosure, accelerating reviews.
-

Enhanced Trust: Cryptographic proofs foster confidence sans identity reveals, contrasting LayerZero‘s policy.
These tools don’t just patch holes; they redefine incentives. Developers flock to protocols with robust, fair systems, accelerating innovation loops.
Platforms like Cantina and zkpoex are proving the model in live DeFi environments. Cantina’s AI sifts through submissions with ruthless efficiency, slashing review times by orders of magnitude while Cantina’s de-duplication catches the duplicates humans miss. zkpoex’s trustless payouts hinge on ZK validity, disbursing funds the moment proofs check out – no committees, no delays. These aren’t theoretical; they’re deployed, hardening protocols against the AI-fueled exploit wave Decrypt warns about.
Pitfalls of Partial Solutions and the Full ZK AI Stack
Yet pitfalls persist. LayerZero’s identity push, while boosting short-term accountability, alienates pseudonymous talent essential to Web3. Aztec Labs’ hefty $450,000 pot draws crowds, but without AI triage, noise drowns signal. ZK patches privacy leaks, AI curbs spam, but silos limit scale. The hybrid stack – ZK for proofs, AI for smarts – unlocks true potential. zkverifiedtasks. com embodies this: AI analyzes task proofs against zkverifiedtasks. com criteria, generating succinct ZK attestations for bounties. Fraud evaporates; only verified work cashes in.
Comparison of Traditional vs. ZK AI Bounty Platforms
| Feature | Traditional (Immunefi) | ZK AI (zkverifiedtasks.com, Cantina, zkpoex) |
|---|---|---|
| Privacy | Low ❌ Privacy concerns and identity risks |
High 🔒 ZK proofs preserve sensitive data |
| Verification Speed | Slow 🐌 Manual delays and bottlenecks |
Fast ⚡ AI + ZK automation |
| Fraud Resistance | Low ❌ AI noise, spam, duplicates |
High 🛡️ AI de-dupe + crypto proofs |
| Auto-Payouts | Manual 👤 Human review required |
Automatic 💰 Trustless on verification |
In my experience steering portfolios through volatility, incomplete hedges invite ruin. DeFi projects ignoring full ZK AI stacks risk the same. Forbes nails it: researcher distrust stems from verification lags. ZK AI dissolves that, fostering ecosystems where hunters invest deeply, unearthing flaws before they bleed TVL.
Future-Proofing DeFi Bounties: AI Agents Meet ZK Identities
Peer ahead: AI agents, armed with ZKPs, autonomously scour codebases. CoinDesk envisions them proving claims sans data dumps, zkSecurity tests their mettle on ZK circuits. Blockchain App Factory charts AI autonomy fortified by proofs across industries; DeFi leads. Imagine swarms of agents submitting verified bugs, scaled globally via StarkWare’s succinctness. Hacken. io’s confidential computations make it feasible, verifying elephantine audits in milliseconds.
Uniswap Technical Analysis Chart
Analysis by Market Analyst | Symbol: BINANCE:UNIUSDT | Interval: 1D | Drawings: 6
Technical Analysis Summary
To annotate this UNIUSDT chart in my balanced technical style, start by drawing a primary downtrend line connecting the swing high at approximately 11.80 on 2026-01-10 to the recent low at 3.00 on 2026-02-04, using the ‘trend_line’ tool with high confidence. Add horizontal support at 3.00 and resistance at 5.50, 7.50 using ‘horizontal_line’. Mark the recent breakdown from consolidation with a ‘vertical_line’ around 2026-01-28. Use ‘fib_retracement’ from the major high to low for potential retracement levels at 23.6% (4.20), 38.2% (5.10), and 50% (6.40). Highlight entry zone near 3.20 with ‘long_position’ icon, profit target at 5.50 and stop at 2.80 using ‘order_line’. Add callouts for declining volume and bearish MACD crossover. Finally, rectangle the late-Jan consolidation zone between 3.50-4.50 from 2026-01-20 to 2026-01-28.
Risk Assessment: medium
Analysis: Bearish trend intact but oversold signals and DeFi ZK news tailwinds suggest measured long opportunities; medium tolerance fits scalp trades.
Market Analyst’s Recommendation: Consider long entries near 3.20 with tight stops, target 5.50; monitor volume for confirmation.
Key Support & Resistance Levels
📈 Support Levels:
-
$3 – Strong multi-touch low with wick rejection, key bottom.
strong -
$4.2 – Minor support from fib 23.6% retracement.
weak
📉 Resistance Levels:
-
$5.5 – Recent swing low turned resistance.
moderate -
$7.5 – Mid-channel resistance from prior consolidation.
strong
Trading Zones (medium risk tolerance)
🎯 Entry Zones:
-
$3.2 – Bounce from strong support with potential bullish divergence.
medium risk
🚪 Exit Zones:
-
$5.5 – First resistance target, fib 38.2% extension.
💰 profit target -
$2.8 – Below key support invalidates long setup.
🛡️ stop loss
Technical Indicators Analysis
📊 Volume Analysis:
Pattern: declining on downmove
Bearish volume drying up near lows, suggesting weakening sellers.
📈 MACD Analysis:
Signal: bearish crossover but histogram contracting
MACD line below signal with potential bullish divergence.
Applied TradingView Drawing Utilities
This chart analysis utilizes the following professional drawing tools:
Disclaimer: This technical analysis by Market Analyst is for educational purposes only and should not be considered as financial advice.
Trading involves risk, and you should always do your own research before making investment decisions.
Past performance does not guarantee future results. The analysis reflects the author’s personal methodology and risk tolerance (medium).
Challenges linger – proof generation compute, AI bias – but Epicenter’s ZK ML secures the stack. zkverifiedtasks. com pioneers bounty bounties here, verifying AI-driven tasks with zk proofs. Opinion: this isn’t incremental; it’s exponential. Protocols adopting now command premium talent, outpacing rivals in security and speed. Bounty programs DeFi verification evolves from bottleneck to flywheel.
DeFi’s frontier demands tools matching its ambition. Privacy-focused ZK AI tech scales bounty programs without compromise, turning vulnerability hunts into strategic moats. Projects wielding these – from zkpoex’s proofs to Cantina’s filters to zkverifiedtasks. com’s full suite – don’t just survive hacks; they thrive amid them. Whitehats, unmasked risks, and frictionless rewards draw the best, fueling unbreakable protocols. The shift is underway; savvy teams will lead it.