Verifiable Compute for Off-Chain Bounty Tasks Proven On-Chain

In the sprawling ecosystem of Web3 bounties, where developers chase rewards for solving complex tasks, fraud lurks in the shadows of unverified claims. Imagine a bounty hunter submitting code for a smart contract audit, only for duplicates or fabrications to dilute the prize pool. Enter verifiable compute: a paradigm that delegates heavy off-chain computations to untrusted parties while anchoring their correctness on-chain via zero-knowledge proofs. This isn’t just theory; it’s reshaping verifiable compute bounties, ensuring only legitimate zk proofs task verification unlocks payouts.

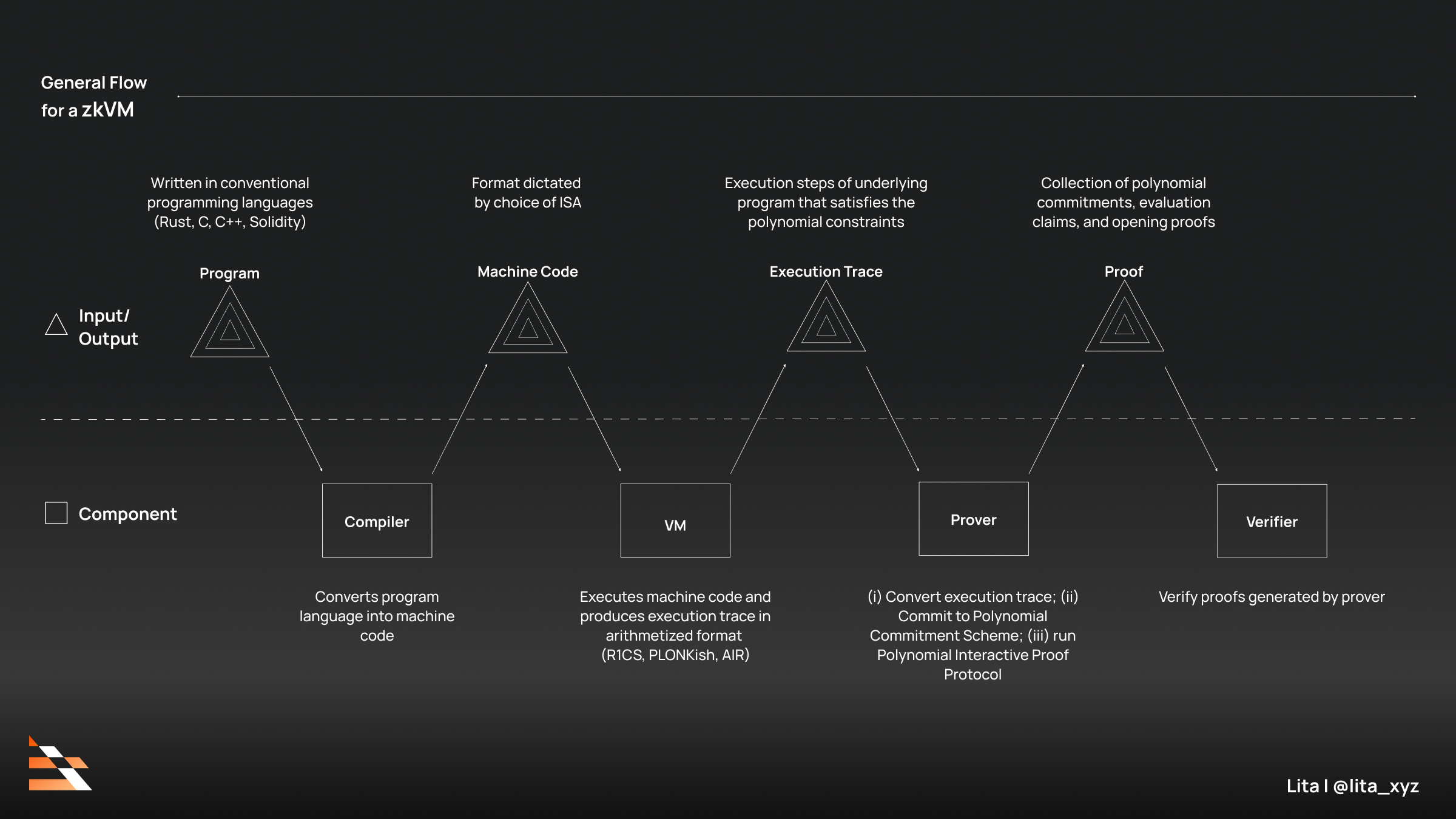
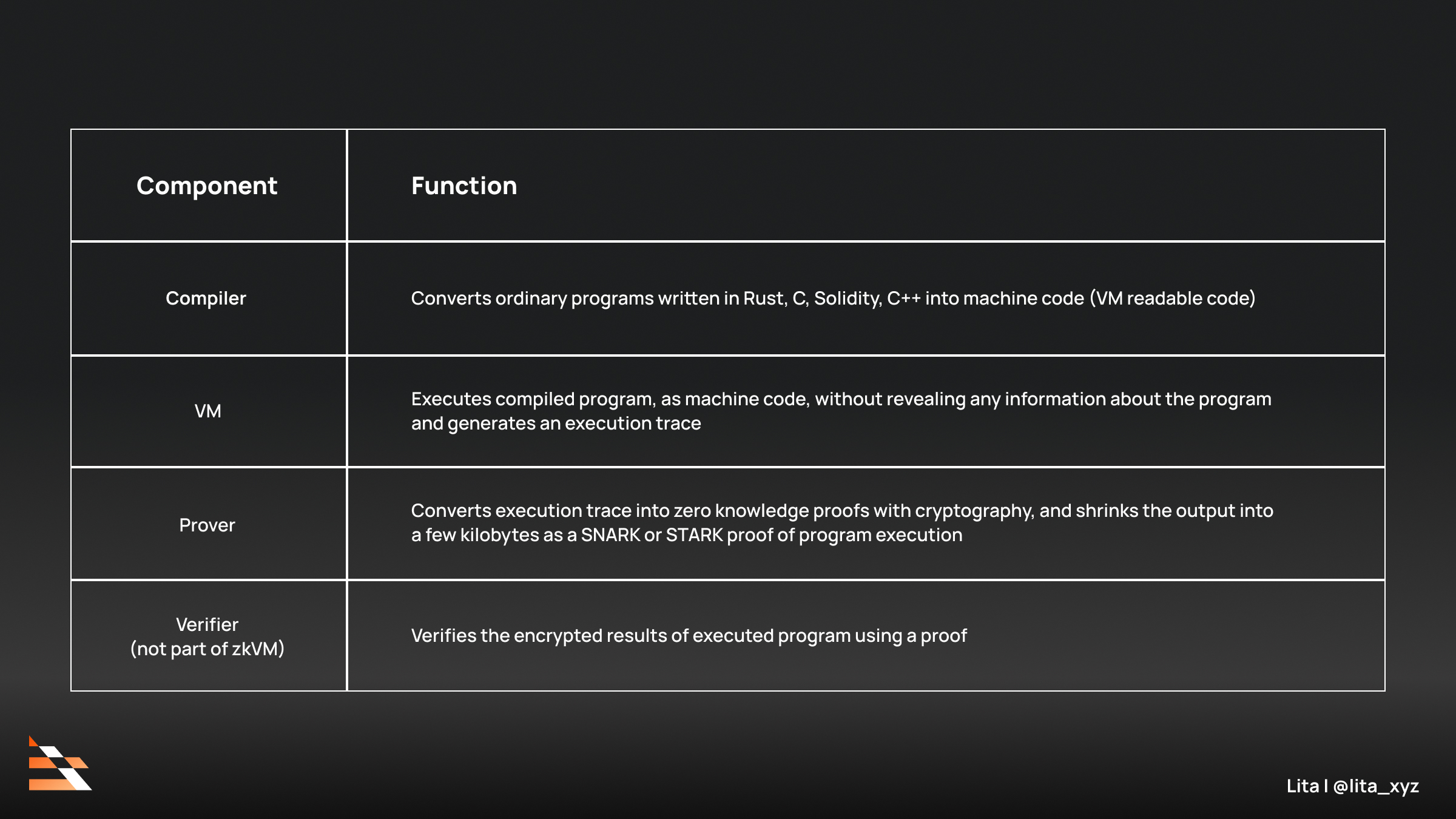
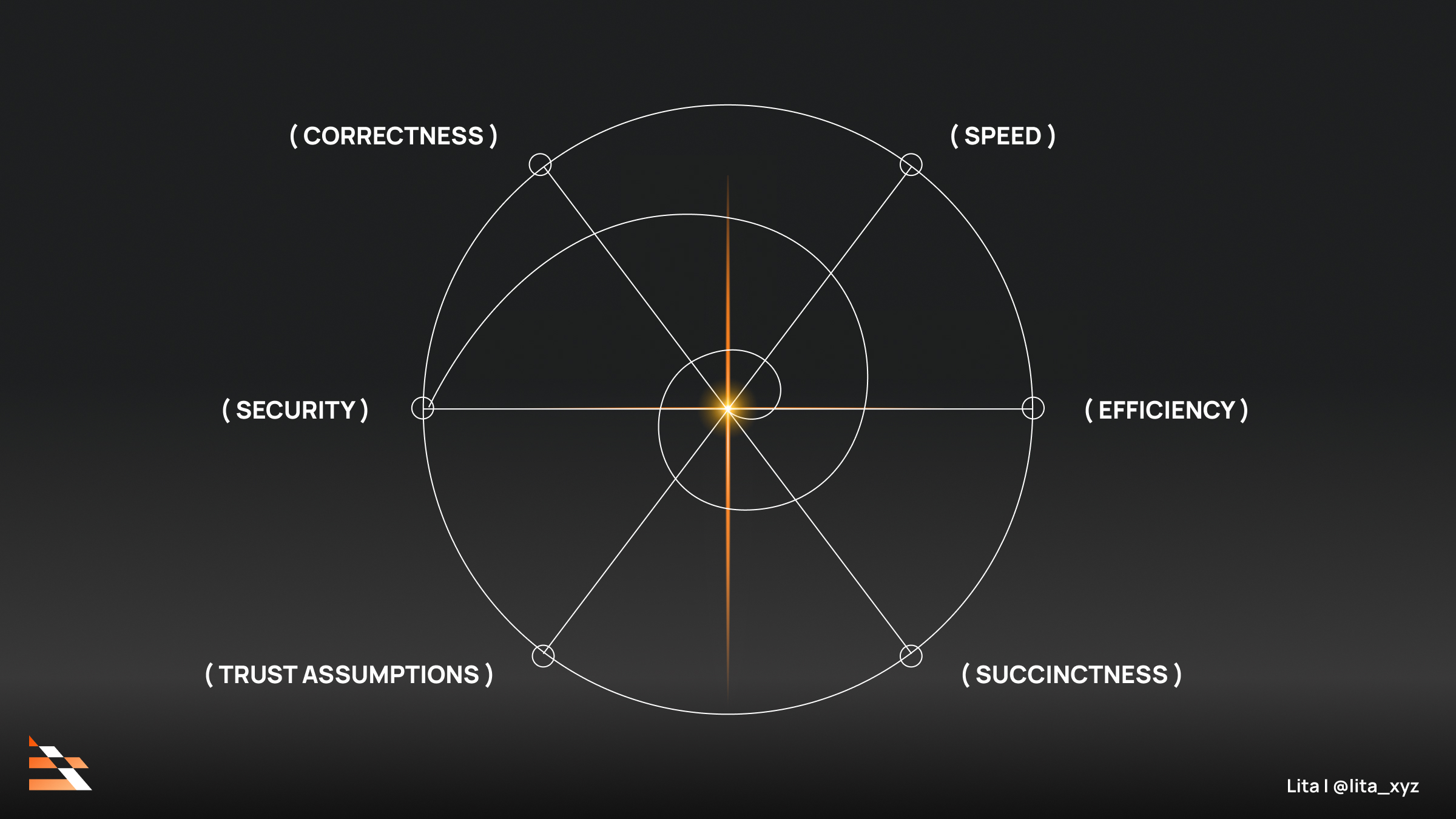
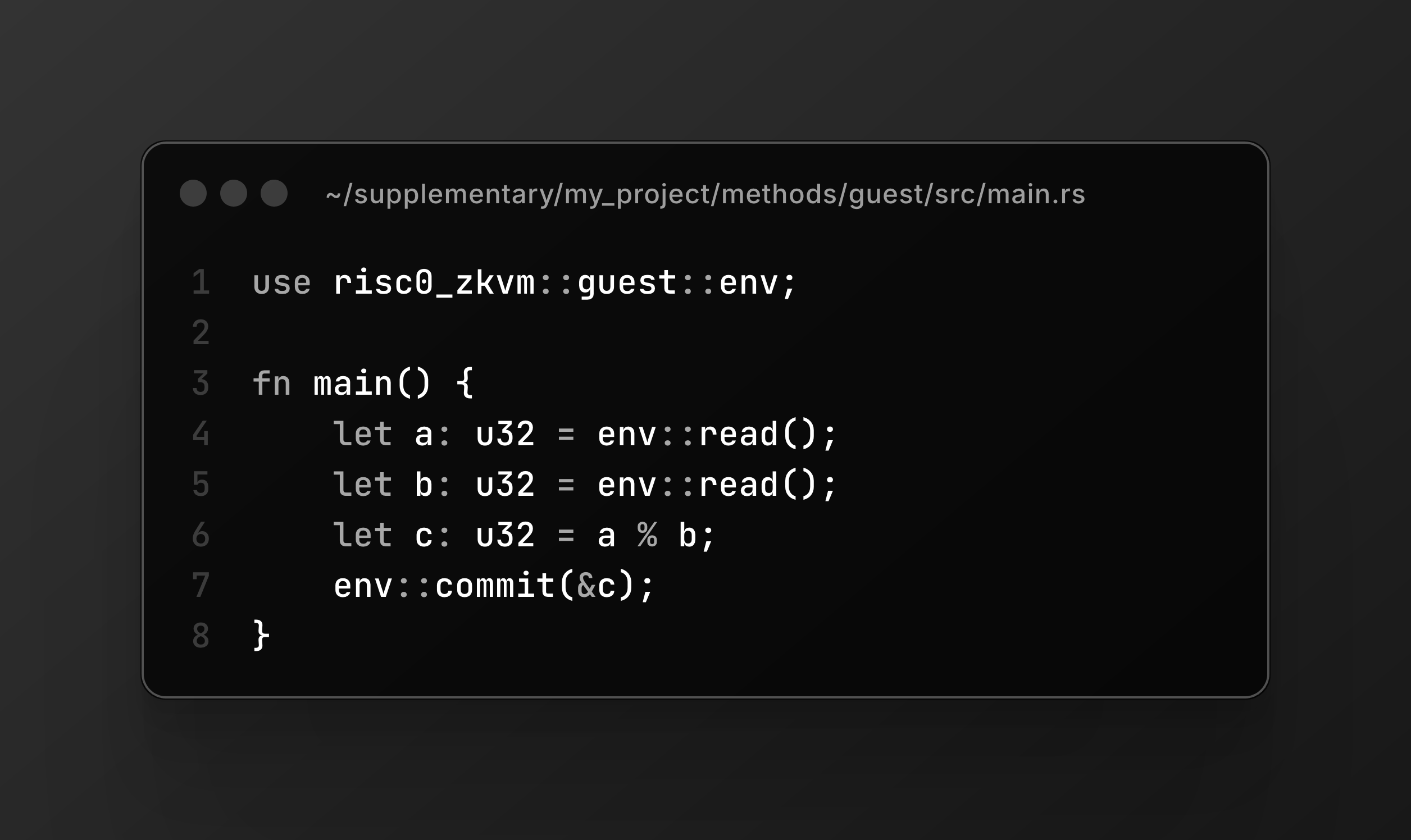
At its core, verifiable compute tackles blockchain’s eternal scalability bind. Blockchains excel at transparency but falter under compute-intensive workloads like AI model inferences or intricate simulations needed for bounties. Offloading these to zkVMs – zero-knowledge virtual machines – allows execution anywhere, with proofs compressing the effort into succinct on-chain checks. Projects like RISC Zero pioneer this, promising cryptographic certainty that outputs match inputs, regardless of the prover’s intent. No more blind trust in bounty submissions; proofs enforce honesty.
The zkVM Revolution Powering Off-Chain Proofs
zkVMs represent a maturation in ZK verifiable computing, evolving from L2 zkRollups that bundled transactions, to coprocessors handling arbitrary logic, and now toward L1 zkEVMs embedding proofs natively. This trajectory, as chronicled in analyses from a16z crypto and BroadNotes, accelerates the “world computer” by shunting expensive ops off-chain. For zkVM web3 tasks, Rust compatibility in RISC Zero lowers barriers, letting developers leverage familiar crates while generating proofs that auditors can’t dispute.
Yet, challenges persist. A HackenProof report flagged a constraint lapse in early RISC Zero iterations, underscoring the need for rigorous prover isolation. Recent fixes and competitors like Succinct bolster resilience, making off-chain proof on-chain bounties viable for real stakes. Succinct’s infrastructure, lauded by Binance, scales DeFi and AI alike, verifying proofs in milliseconds – a boon for time-sensitive bounties.
Bridging Bounties with ZK: Remedy and Beyond
Bug bounty platforms like Remedy exemplify the fusion. Their ZK tech detects duplicate submissions without exposing sensitive strategies, a game-changer for security researchers. As JohnnyTime’s coverage notes, hefty rewards await those proving exploits, with proofs ensuring uniqueness. This mirrors broader trends: ZKaggleV2 monetizes private ML models via succinct proofs, empowering bounty hunters to claim credits credibly.
Key zkVM Advantages
-
Privacy Preservation: zkVMs leverage zero-knowledge proofs (ZKPs) to verify computations without revealing sensitive inputs or data, protecting confidential bounty task details. (Lita Foundation)
-

Fraud Elimination: Cryptographic proofs ensure off-chain bounty task results are correct and untampered, eliminating cheating or false submissions with on-chain verifiability. (RISC Zero)
-
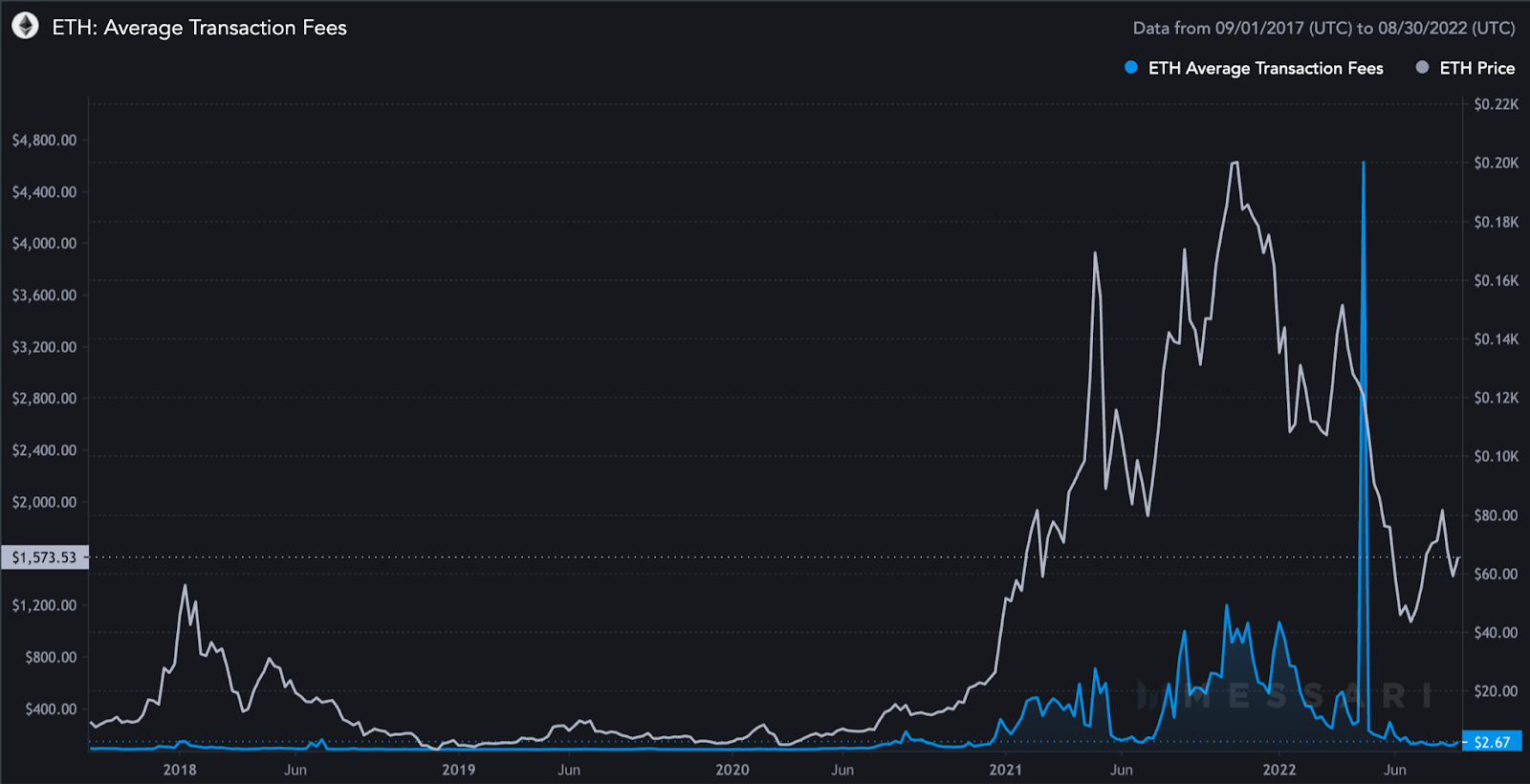
Scalability Boost: Offloads heavy computations off-chain while lightweight proofs verify on-chain, enabling massive scaling for complex bounty tasks without blockchain congestion. (a16z crypto)
-
Cost Efficiency: Reduces verification costs dramatically—e.g., 8x cheaper for attestations—making frequent bounty payouts affordable via succinct proofs. (Automata Network)
Updated advancements amplify this. Chainlink Automation 2.0’s verifiable compute layer offloads via OCR 3.0 consensus, slashing on-chain gas. Bonsol tailors it for Solana’s high throughput, balancing proof speed with verifiability. Meanwhile, Agora’s Polkadot parachain outsources via staked workers, verified through commit-reveal and XCM. zk-Oracle and TCUs generalize further, proving heterogeneous computes across chains.
Why Verifiable Compute Wins for Bounty Ecosystems
Consider the economics: traditional bounties waste resources on manual reviews, prone to collusion. Verifiable compute flips the script, automating trust. A zkVM executes a task – say, fuzzing a protocol for vulns – generates a proof, and submits it on-chain. Platforms like zkverifiedtasks. com can slash rewards only to valid proofs, curbing spam while preserving privacy. No revealing proprietary test vectors; just mathematical certainty.
This isn’t hype; Automata Network’s zkVM for TEEs cuts attestation costs 8x, integrating TLS proofs for data feeds bounties rely on. Lita Foundation frames zkVMs as privacy guardians, ideal for competitive arenas where strategies stay secret. For developers and hunters, it means faster payouts, broader participation, and ironclad integrity – fundamentals that endure market cycles.
Platforms like zkverifiedtasks. com stand at the vanguard, fusing AI scrutiny with zk proofs for seamless zk proofs task verification. Here, bounties aren’t gambled on subjective audits; AI parses submissions for completeness, then zkVMs cryptographically seal authenticity. This hybrid approach – intelligent yet unassailable – mirrors disciplined portfolio construction: layer analysis atop proofs for compounded reliability.
Delve deeper into the mechanics. A bounty hunter tackles an off-chain proof on-chain bounties task, like simulating DeFi liquidations under stress. Their zkVM runtime, perhaps Succinct’s SP1 or RISC Zero’s zkVM, ingests inputs, computes outputs, and spits a proof attesting, “This happened, exactly as specified. ” On-chain, a verifier contract checks it in seconds, disbursing funds sans disputes. No central arbiter; math arbitrates.
Real-World Deployments: From Solana to Polkadot
Bonsol exemplifies Solana-specific finesse, verifying diverse proofs without bloating blocks. Developers offload GPU-heavy tasks – think ML bounties for anomaly detection – reclaiming native speed. Across ecosystems, Agora’s parachain model stakes workers on correctness, slashing invalid claims via XCM bridges. Chainlink’s OCR 3.0 consensus adds redundancy, ideal for oracle-dependent bounties where data freshness trumps all.
TCUs push boundaries further, compositing proofs from TEEs, zkVMs, and beyond. Imagine a bounty chaining AI inference (zkML) to vulnerability scans; TCUs orchestrate, proving the pipeline end-to-end. zk-Oracle complements by attesting off-chain data fetches, vital for real-world bounties like climate model validations. These aren’t silos; they’re interoperable primitives building a verifiable compute bazaar.
Skeptics might counter: proofs remain costly, even compressed. Fair point, but recursion and aggregation – as in Succinct’s proofs – amortize this. Early RISC Zero hiccups taught humility, yet iterative hardening yields proofs under 1MB, verifiable for pennies. For high-value bounties, this trumps manual overhead. Privacy seals the deal: competitors glimpse nothing beyond proof validity, fostering aggressive innovation without IP leaks.
Investment Lens on zkVM Web3 Tasks
From my vantage as a CFA charterholder navigating cycles, verifiable compute echoes value investing tenets. Markets punish speculation; bounties punish fraud. zkVMs impose fundamentals-first discipline, rewarding signal over noise. Blue-chip protocols like Chainlink integrate it natively, signaling maturity. Emerging plays – Remedy’s bounty wars, zkverifiedtasks. com’s AI-zk nexus – offer asymmetric upside for early allocators, much like spotting undervalued bonds pre-rally.
Picture a portfolio of bounties: diversify across zkML predictions, security audits, data labeling. Verifiable compute automates rebalancing, slashing deadweight. Risk management? Staking slashes cheaters, akin to margin calls. Long-term, as L1 zkEVMs mature, on-chain verification becomes ambient, turbocharging Web3’s compute layer. Patience pays; those ignoring zkVMs risk obsolescence, watching fraud erode edges.
Bounty ecosystems thrive on this bedrock. Developers post tasks – optimize a rollup sequencer, verify NFT rarity proofs – hunters prove prowess, platforms payout precisely. zkverifiedtasks. com streamlines it, blending AI triage with zk finality for anti-spam fortification. No more ghost submissions; every claim bears cryptographic weight. This scales participation globally, from solo coders to DAOs, fueling Web3’s meritocracy.
Steps to Launch Verifiable Bounties
-
Define task in zkVM-compatible spec using RISC Zero or Succinct zkVM for off-chain execution with on-chain proofs.
-
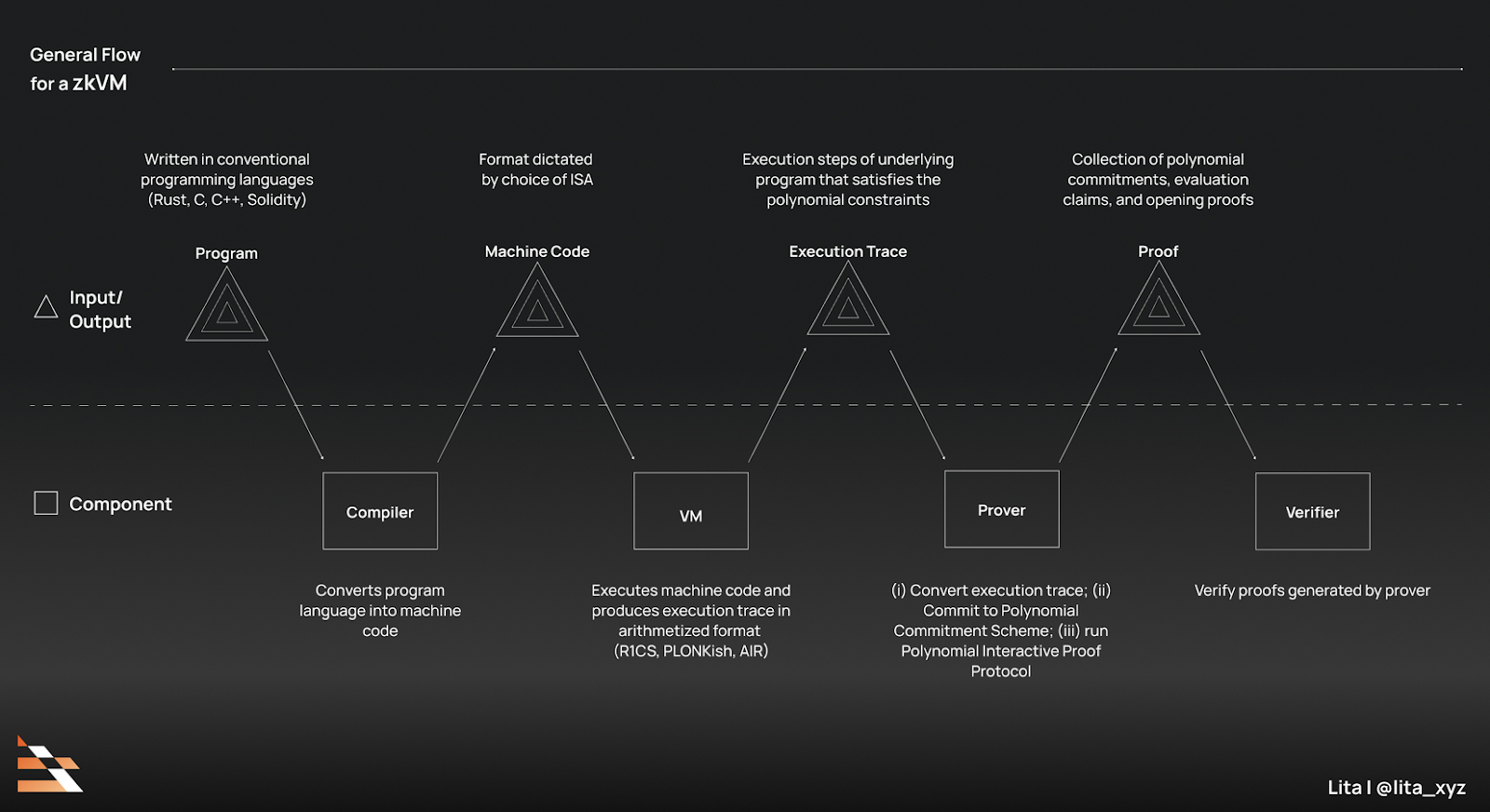
Deploy verifier contract on-chain, e.g., RISC Zero Ethereum verifier or Bonsol for Solana.
-
Integrate AI pre-checks via ZKML frameworks to validate submissions pre-proof.
-

Announce on platforms like Remedy, the ZK-powered bug bounty platform.
-
Monitor proofs via dashboards like RISC Zero Explorer or Chainlink Automation.
Challenges linger – prover centralization, proof times – but momentum crushes them. Automata’s 8x TEE savings, Lita’s privacy paradigms propel adoption. For verifiable compute bounties, the proof is in the protocol: integrity begets growth. Web3 bounties, once chaotic hunts, evolve into precise markets where proofs unlock prosperity. Fundamentals endure; in zkVMs, they’ve found silicon permanence.