AI and ZK Proofs for Fraud-Proof Web3 Bounty Verification in 2026

In the bustling ecosystem of Web3 in 2026, bounty programs promise rich rewards for tasks like bug hunting and content creation, yet fraud lurks around every corner. Sybil attacks, fake submissions, and plagiarized reports drain millions from protocols annually. Enter the tandem of artificial intelligence and zero-knowledge proofs, forging fraud-proof web3 bounty verification that safeguards payouts while honoring privacy. Platforms such as zkverifiedtasks. com pioneer this fusion, leveraging AI for sharp analysis and ZK for cryptographic certainty, turning chaotic bounties into streamlined, trustworthy operations.
Key Advantages of AI ZK Bounties
-
Privacy-preserving verification: ZK proofs confirm bounty completion without revealing sensitive data, as in Extrimian‘s AI-SSI stack and Codezeros fraud detection.
-
Anti-spam task filtering: AI anomaly detection filters invalid submissions, per Cyvers tools and Yeshiva University ML-blockchain study.
-

Instant fraud detection: Real-time AI validation with ZK ensures fraud-proof claims, leveraging Cyvers risk assessment and Proof Certify.
-
Scalable on-chain rewards: ZK enables efficient, low-cost reward payouts on blockchain, supporting high-volume bounties as in Block Trix fraud prevention.
-
Developer-friendly workflows: AI tracking and ZK submissions streamline processes, improving efficiency in Web3 bug bounties per AWS and ResearchGate reviews.
This synergy isn’t mere hype; it’s a measured response to real vulnerabilities. Consider Cyvers’ proactive Web3 security tools, which deploy AI for risk assessment and anomaly detection to shield financial flows. Similarly, research from Yeshiva University highlights how machine learning predicts fraud atop blockchain’s unyielding verification, a blueprint now maturing in bounty contexts. Yet traditional methods falter against sophisticated deepfakes and coordinated spam, demanding more than pattern recognition alone.
Fraud’s Evolving Grip on Bounty Ecosystems
Web3 bounties exploded post-2025, with protocols like BlockBounty adopting ZK proofs for on-chain bug reports, but not without pitfalls. Fraudsters exploit weak verification, submitting bogus vulnerability proofs or inflating task completions via bot farms. A ResearchGate literature review pinpoints emerging patterns: from AI-generated false positives in audits to identity spoofing in KYC-light environments. The Wilson Center underscores this, noting how unverified claims fuel financial fraud, echoing cryptocurrency scams where provers mislead without repercussions.
What troubles me most, after years dissecting markets for fundamental flaws, is the noise these scams create. Legitimate hunters waste time amid fakes, eroding trust. Tools like Arguzz, testing zkVMs for soundness, reveal even ZK systems harbor bugs if unvetted. Without layered defenses, bounties devolve into lotteries, not meritocracies.
AI’s Precision in Task Scrutiny
Artificial intelligence steps in as the vigilant gatekeeper for AI zk proofs bounties. By 2026, models trained on vast on-chain datasets flag anomalies with surgical accuracy. Extrimian’s AI-SSI stack, for instance, slashes fraud across industries through zero-knowledge integration, proving its mettle in bounty verification. AWS insights further reveal adaptive AI agents evolving against deepfake scams, vital for vetting video proofs or code snippets in bounties.
Picture this: an AI scans a submitted report, cross-referencing code diffs against repositories, scoring semantic similarity to detect plagiarism. It validates transaction histories without exposing wallets, aligning with Proof. com’s Certify platform that merges fraud detection and notarization. In zkverifiedtasks. com’s workflow, this means rapid triage, prioritizing genuine zk proofs secure bounties for human review only when needed.
Opinionated take: AI alone risks overreach, hallucinating flags on novel bugs, but paired with blockchain’s ground truth, it shines. Codezeros notes how ZK powers AI integrity in Web3, enabling private fraud models on confidential data, a game-changer for competitive bounties where strategies stay hidden.
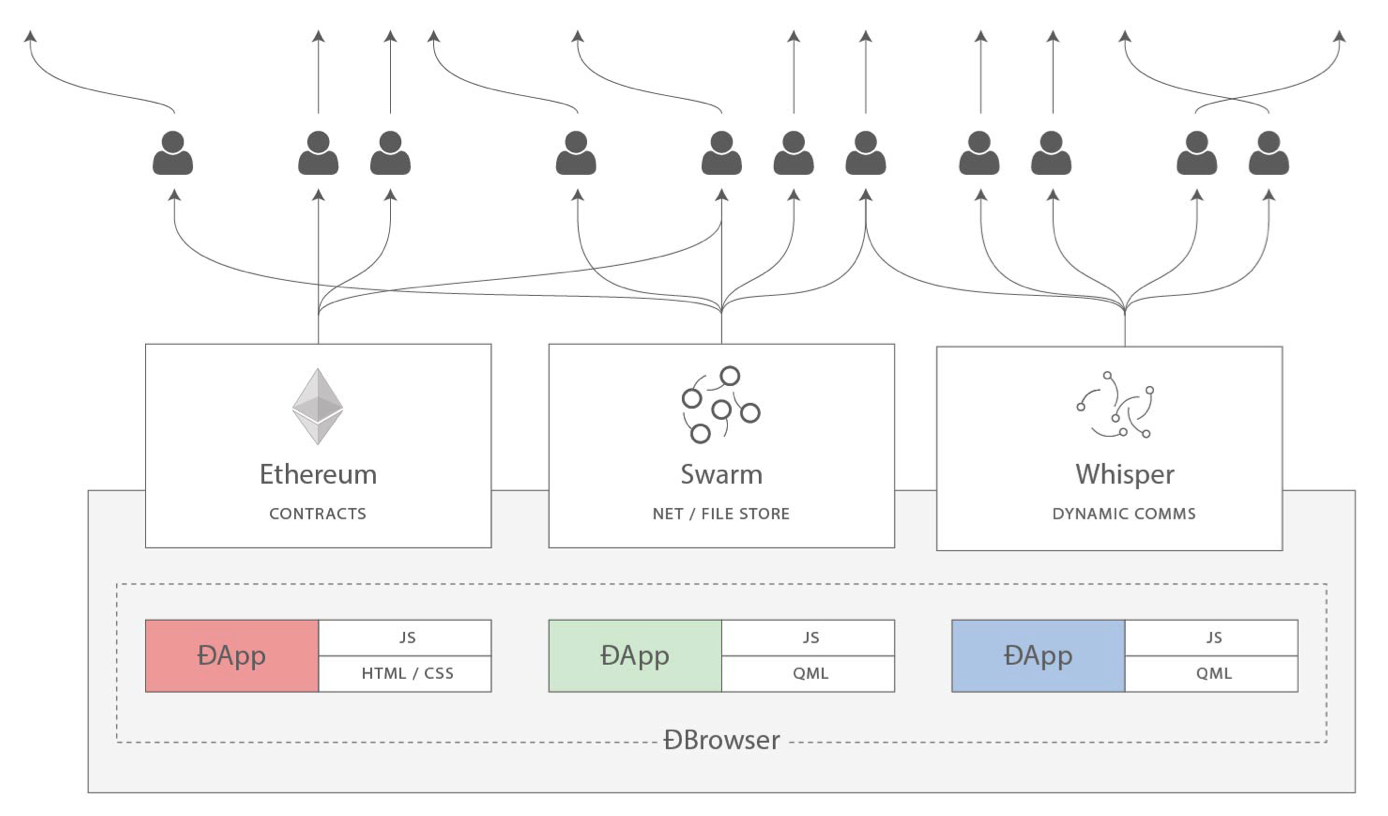
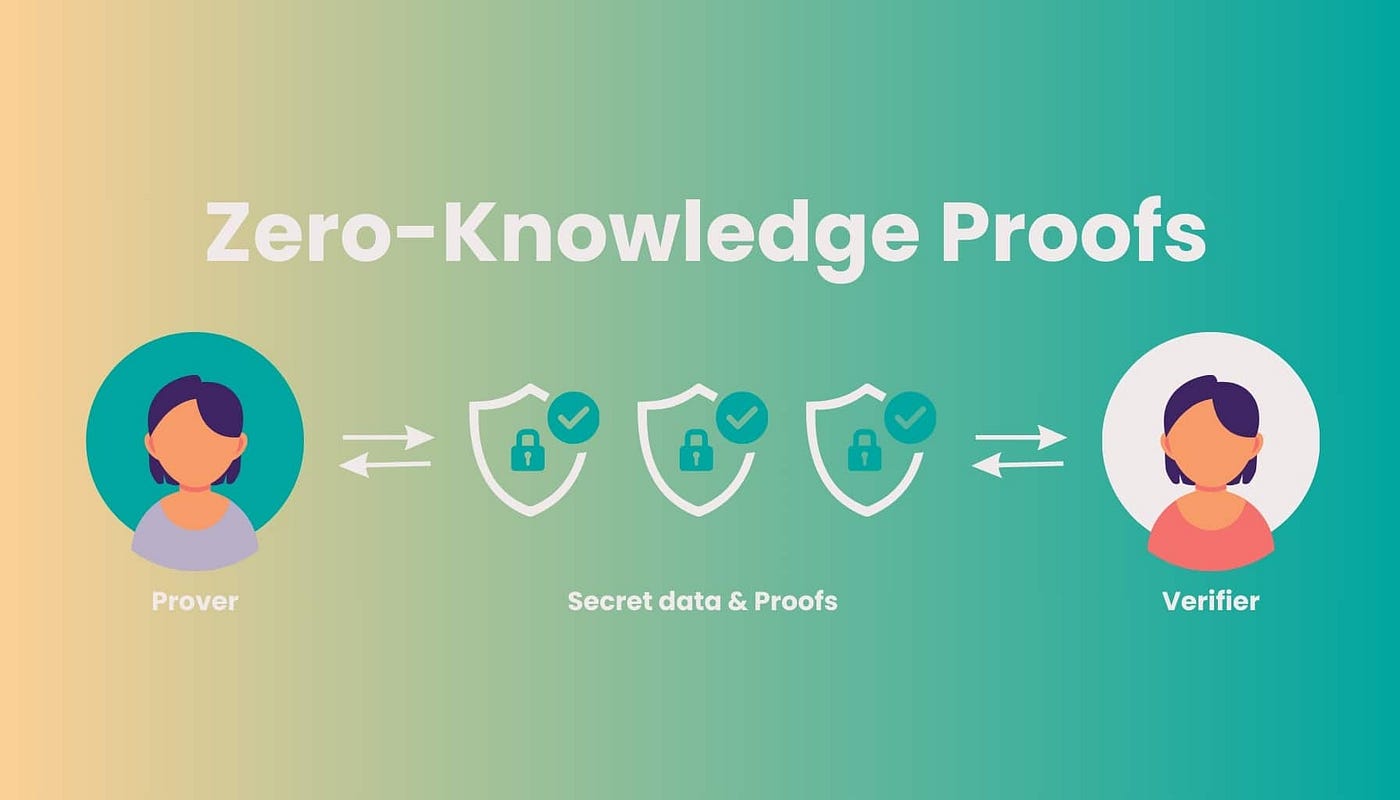
Zero-Knowledge Proofs Locking in Trust
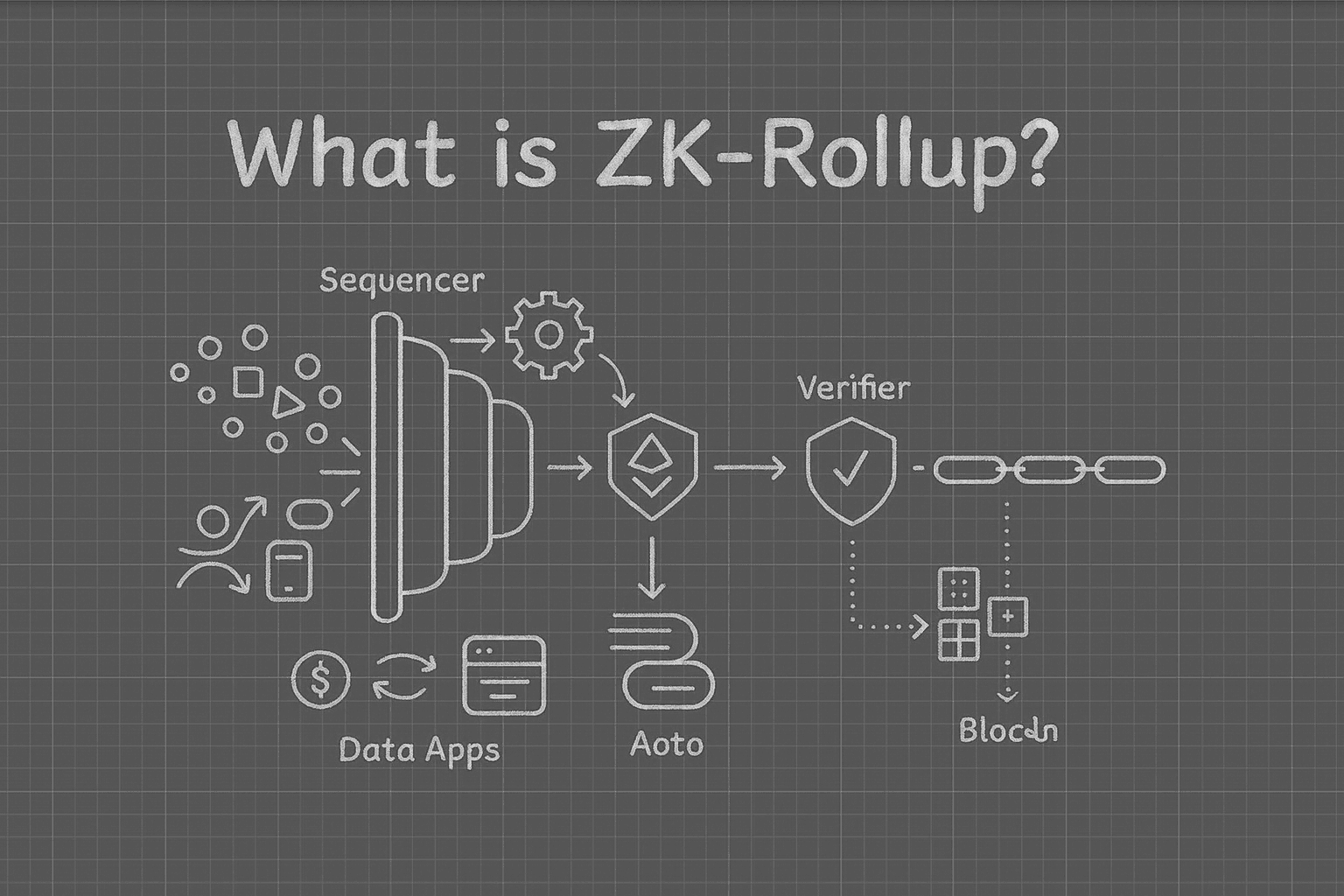
Zero-knowledge proofs elevate verification from probable to provable, central to AI task completion proofs web3. A prover attests task completion – say, finding a smart contract exploit – without revealing the method, verifiable on-chain. Block Trix explains this fraud prevention: the prover can’t cheat, as invalid proofs fail mathematically.
In 2026’s landscape, zkVerify extends this to AI itself, verifying model inferences privately. Bounty platforms embed ZK circuits proving task metrics met thresholds, like code coverage or exploit reproducibility, all while masking sensitive details. Medium’s Adeola David captures the essence: ZK unlocks privacy in finance fraud detection, now rippling to bounties for auditable, efficient claims.
Platforms like zkverifiedtasks. com operationalize this by generating ZK proofs for task completion, where AI first assesses submissions off-chain before the proof crystallizes validity on-chain. This fraud proof task verification web3 model minimizes gas fees while maximizing certainty, a fundamental shift from probabilistic scoring to ironclad math.
I’ve long preached patience in investments, sifting signal from noise. Here, AI filters the din, ZK provides the proof – a duo that rewards merit over manipulation. Yet integration demands rigor; Arguzz’s zkVM audits exposed early soundness gaps, underscoring the need for continuous hardening.
Real-World Wins and Hurdles Ahead
By early 2026, adoption surges. Extrimian’s case studies show industries halving fraud with AI-SSI-ZK stacks, now adapted for bounties. Proof. com’s Certify fuses notarization and detection, inspiring platforms to verify AI-generated reports cryptographically. On-chain games benefit too, per Codezeros, where ZK-AI ensures fair play in task-based economies without exposing strategies.
Challenges persist, analytically speaking. ZK proof generation remains compute-intensive, though 2026’s zkVM optimizations – vetted by Arguzz – cut times by 70%. AI model drift poses risks, but zkVerify’s verifiable inference counters this, attesting outputs match training data privately. Scalability hinges on layer-2 rollups, yet the privacy payoff justifies it: hunters retain competitive edges in a cutthroat arena.
Opinion creeps in: skeptics decry complexity, but fundamentals win. Traditional bounties bleed value to fraud; this stack preserves it, much like dividend aristocrats weather volatility. AWS’s adaptive agents evolve defenses against deepfakes, ensuring video proofs hold water. ResearchGate’s fraud patterns evolve, yet ZK’s math endures. zkverifiedtasks. com stands at the vanguard, blending these forces into developer-friendly bounties. Bug hunters submit securely, creators claim rewards sans exposure, protocols pay precisely. As Web3 matures, this web3 bounty verification paradigm cements trust, channeling talent into innovation over infighting. The result? Ecosystems that scale not despite fraud, but because it’s obsolete.