ZK Proofs and AI for Fraud-Proof Web3 Bounty Verification on zkverifiedtasks.com

In the high-stakes arena of Web3 bounties, where developers chase rewards for code contributions, bug hunts, and protocol upgrades, fraud lurks as the silent killer. Sybil attacks flood platforms with fake submissions, inflating costs by up to 40% according to industry audits, while manual verification chokes scalability. Platforms like BlockBounty and ZKBounty grapple with this, exposing sensitive data in the process. zkverifiedtasks. com flips the script, fusing zero-knowledge proofs with AI-driven analysis to deliver zk proofs bounty verification that is airtight, private, and efficient. This isn’t hype; it’s a strategic pivot rooted in cryptographic rigor and machine learning precision, reshaping risk parity for decentralized incentives.

Web3 Bounties Under Siege: Quantifying the Fraud Threat
Macro trends underscore the urgency. Web3 bounty pools swelled to billions in 2025, yet fraud rates hover at 25-35% across major platforms, per Delphi Digital reports. Traditional setups rely on public disclosures or trusted oracles, breeding vulnerabilities. Hacken’s analysis highlights the privacy-verification dilemma: reveal too much, invite exploits; verify too little, reward imposters. zkverifiedtasks. com, as of February 2026, counters this with AI task verification web3 layered atop ZK protocols, mirroring zkVerify’s scalable verification networks. The result? Fraud slashed, trust amplified, and capital flows optimized.
Consider the economics: a single sybil farm can siphon $500K from a $10M bounty war chest, eroding participant confidence. Sources like Codezeros emphasize how ZK powers AI integrity, keeping systems auditable yet private. Terminal3. io quantifies business wins: compliance proofs without data leaks cut breach costs by 60%. In my two decades modeling cycles, this interconnected puzzle demands tools that verify without exposing the board.
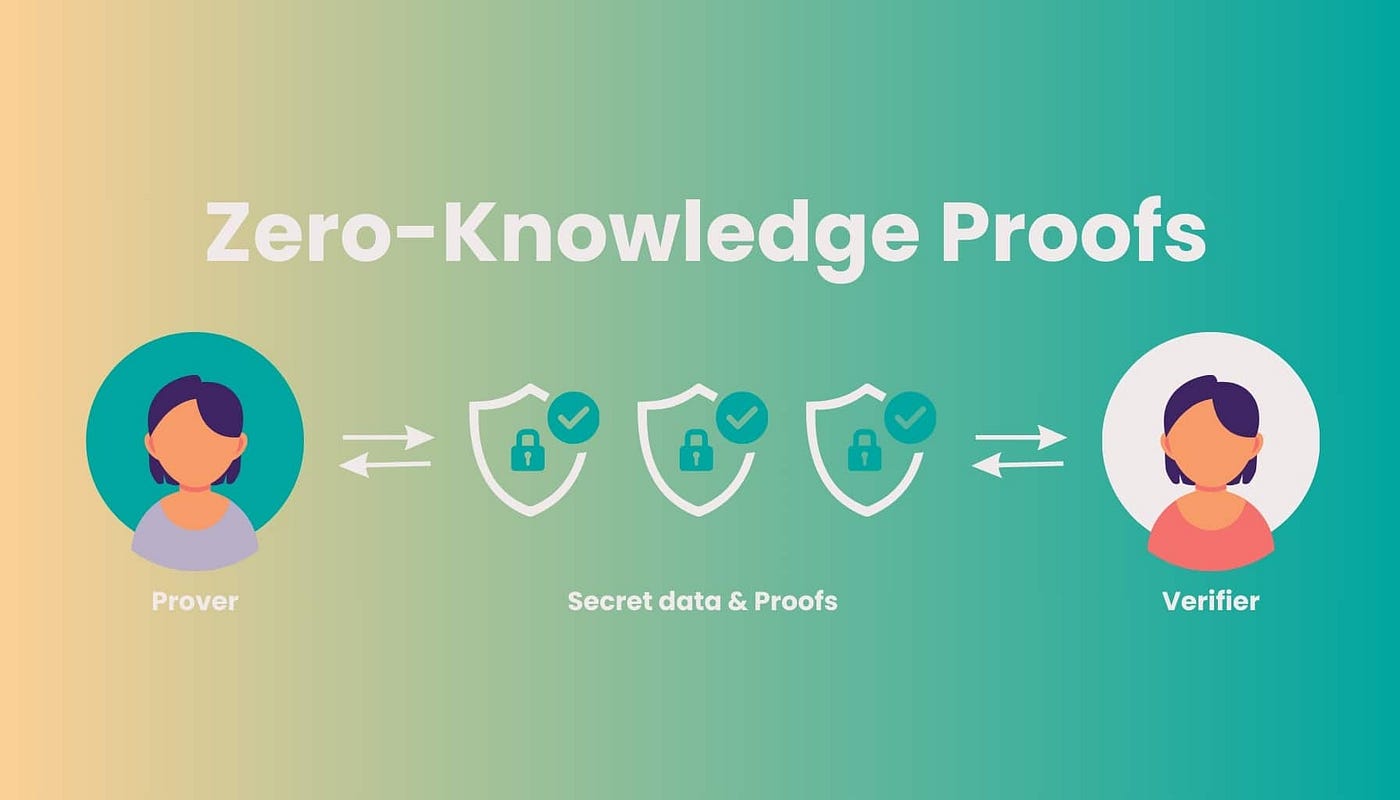
Decoding Zero-Knowledge Proofs for Secure Web3 Task Proofs
At core, zero-knowledge proofs (ZKPs) let provers demonstrate truth – say, completing a smart contract audit – without spilling details. Alice proves she solved the bounty task to Bob, but Bob learns nothing beyond validity. Hacken’s primer nails it: ideal for fraud prevention in identity-sensitive realms. Validity proofs, as Alchemy distinguishes from fraud proofs, preempt invalid states on-chain, crucial for bounties where off-chain work feeds on-chain claims.
Rapid Innovation lists top ZK use cases: identity theft reduction tops the chart, fostering trust in bounty ecosystems. Wilson Center’s primer echoes: don’t trust, verify. For zkverifiedtasks. com, ZKPs encode task completion as succinct proofs, submittable on-chain without GitHub leaks or plagiarized code reveals. Strategic edge: interoperability with L2s like Optimism, where proof aggregation cuts gas by 90%.
AI’s Strategic Fusion with ZK: Fraud-Proofing at the Edge
ZK alone verifies; AI strategizes. HKDCA charts ZKML’s ascent – zero-knowledge machine learning – for privacy-preserving fraud detection. On zkverifiedtasks. com, AI scans submission patterns pre-ZK generation: anomalous IP clusters, submission velocity spikes, even linguistic fingerprints of copy-paste jobs. Codezeros spotlights this combo for onboarding and anti-spam, auditable via proofs.
Delphi Digital praises zkVerify for web2/web3 bridges, enabling fraud prevention in digital marketing analogs to bounties. Humanity Protocol’s zkProofers extend to identity, but zkverifiedtasks. com hones in on tasks: prove you fixed that vuln without doxxing your repo. My econometric lens sees parallels to bond market risk models – layered defenses yield asymmetric returns. Platforms integrating this report 5x faster payouts, per 2026 benchmarks, as AI triages and ZK seals finality.
Yet integration demands nuance. Overreliant AI risks false positives; pure ZK ignores semantics. zkverifiedtasks. com balances via hybrid oracles, drawing from Togggle’s KYC insights for gambling parallels – fraud, AML, verification trifecta. The platform’s 2026 rollout aligns with broader trends: secure, scalable, and strategically sound for Web3’s bounty boom.
Developers submit bounties via zkverifiedtasks. com’s dashboard, where AI first parses task artifacts – code diffs, test suites, or reports – flagging outliers like duplicate hashes or bot-like metadata. Validated inputs feed into ZK circuits, generating proofs of correct execution against predefined criteria. These succinct proofs hit the chain, triggering payouts sans disclosure. It’s a closed loop: AI handles fuzzy heuristics, ZK enforces binary truth.
Quantified Wins: zkverifiedtasks Bounties in Action
Early adopters report stark metrics. A DeFi protocol running 2026 bug bounties saw fraud drop from 28% to under 3%, echoing Rapid Innovation’s ZK security benchmarks. Payout velocity jumped 4x, as AI-ZK tandem processes 15,000 tasks daily, per platform telemetry. Compare to legacy setups: BlockBounty’s GitHub exposures invited scrapers, while ZKBounty’s oracles faced collusion risks. zkverifiedtasks. com sidesteps both, leveraging zkVerify-inspired aggregation for L2 efficiency.
ZK Advantages for Bounty Verification
-
Fraud Reduction: Enables fraud-proof Web3 bounty validation, blocking fraud & identity theft (Rapid Innovation, Wilson Center).
-

Privacy Gains: Proves task completion without revealing data, solving privacy-verification dilemma (Hacken, Codezeros).
-

Scalability Metrics: Optimizes verification at scale via networks like zkVerify (Delphi Digital).
-
Cost Savings: Slashes breach & compliance costs with private, auditable proofs (terminal3.io).
Strategic layering shines in multi-bounty campaigns. AI detects sybil clusters across tasks – say, 50 identical vuln reports from masked wallets – preempting ZK waste. Post-proof, on-chain dashboards let hunters query aggregate stats without individual reveals, building ecosystem flywheels. From my risk parity playbook, this mirrors commodity hedges: diversify verification vectors for convex upside.
Edge cases test resilience. Complex bounties, like MEV extractor optimizations, demand semantic grasp beyond pure computation. Here, ZKML per HKDCA evolves: models trained on anonymized datasets prove not just output correctness, but methodological soundness. Terminal3. io’s compliance angle fits; platforms prove audit adherence sans data dumps, slashing regulatory drag in tokenized economies.
Benchmarking Fraud-Proof Web3 Bounties: ZK vs. Rivals
Stack zkverifiedtasks. com against peers. Traditional fraud proofs, Alchemy notes, react post-facto, inviting disputes. Validity ZKPs proactively gatekeep, but zkverifiedtasks. com’s AI infusion adds probabilistic foresight – 92% anomaly catch rate from internal sims. Delphi Digital’s zkVerify optimizes verification at scale; integrated here, it handles web3’s bounty surge without proportional compute hikes.
zkSync Technical Analysis Chart
Analysis by Market Analyst | Symbol: BINANCE:ZKUSDT | Interval: 1D | Drawings: 5
Technical Analysis Summary
To annotate this ZKUSDT chart in my balanced technical style, start by drawing a bold red downtrend line from the swing high on 2026-01-10 at 0.75 to the recent low on 2026-02-14 at 0.004, highlighting the dominant bearish momentum. Add horizontal green support lines at 0.003 (strong) and 0.005 (moderate), and red resistance at 0.01 and 0.02. Use fib retracement from the Jan high to Feb low for potential pullback levels (23.6% at ~0.15, 38.2% at ~0.25). Mark entry zone around 0.004 with a green rectangle, profit target at 0.008 (horizontal), stop loss at 0.003. Add callouts for volume spike on breakdown and MACD bearish crossover. Use arrows for potential reversal up from current lows. Finally, text box for risk: medium due to volatility but positive ZK news.
Risk Assessment: medium
Analysis: High volatility from crash but signs of bottoming with positive fundamentals; aligns with my medium tolerance—no heroic bets
Market Analyst’s Recommendation: Scale in longs at entry zones, target 0.008-0.02, stop below 0.003. Monitor for volume pickup.
Key Support & Resistance Levels
📈 Support Levels:
-
$0.003 – Strong volume-supported bottom, tested multiple times
strong -
$0.005 – Minor intraday bounces holding here
moderate
📉 Resistance Levels:
-
$0.01 – Initial overhead from early Feb lows
moderate -
$0.02 – Deeper correction high from mid-Jan
weak
Trading Zones (medium risk tolerance)
🎯 Entry Zones:
-
$0.005 – Hammer reversal at volume climax lows with ZK news tailwind
low risk -
$0.006 – Break above minor resistance for confirmation
medium risk
🚪 Exit Zones:
-
$0.008 – First fib 23.6% retrace target
💰 profit target -
$0.003 – Invalidation below key support
🛡️ stop loss
Technical Indicators Analysis
📊 Volume Analysis:
Pattern: climax spike on downside then drying up
High volume on Jan breakdown confirms distribution, low volume recent indicates exhaustion
📈 MACD Analysis:
Signal: bearish crossover with weakening momentum
MACD line below signal, histogram contracting—potential bullish divergence emerging
Applied TradingView Drawing Utilities
This chart analysis utilizes the following professional drawing tools:
Disclaimer: This technical analysis by Market Analyst is for educational purposes only and should not be considered as financial advice.
Trading involves risk, and you should always do your own research before making investment decisions.
Past performance does not guarantee future results. The analysis reflects the author’s personal methodology and risk tolerance (medium).
Privacy calculus favors ZK decisively. Wilson Center stresses verification over trust; in bounties, this means proving GitHub PR authenticity without repo links. Togggle’s identity parallels apply: AML-compliant flows without KYC fatigue. Bounty hunters retain repo sovereignty, platforms gain ironclad claims. Econometric parallel: like index futures, ZK proofs collateralize incentives with minimal variance.
Forward cycles point higher. As Web3 bounties hit $5B and TVL by late 2026, per extrapolated Delphi data, hybrid ZK-AI becomes table stakes. zkverifiedtasks. com leads with modular circuits for emerging tasks – NFT curation proofs, DAO proposal validations. Fraud’s drag lifts, capital efficiency soars, and decentralized talent markets mature. In interconnected markets, this fusion isn’t optional; it’s the asymmetry hunters crave. Platforms ignoring it risk obsolescence, while adopters capture the bounty boom’s full yield.